1/ Welcome to the Circle $USDC files.
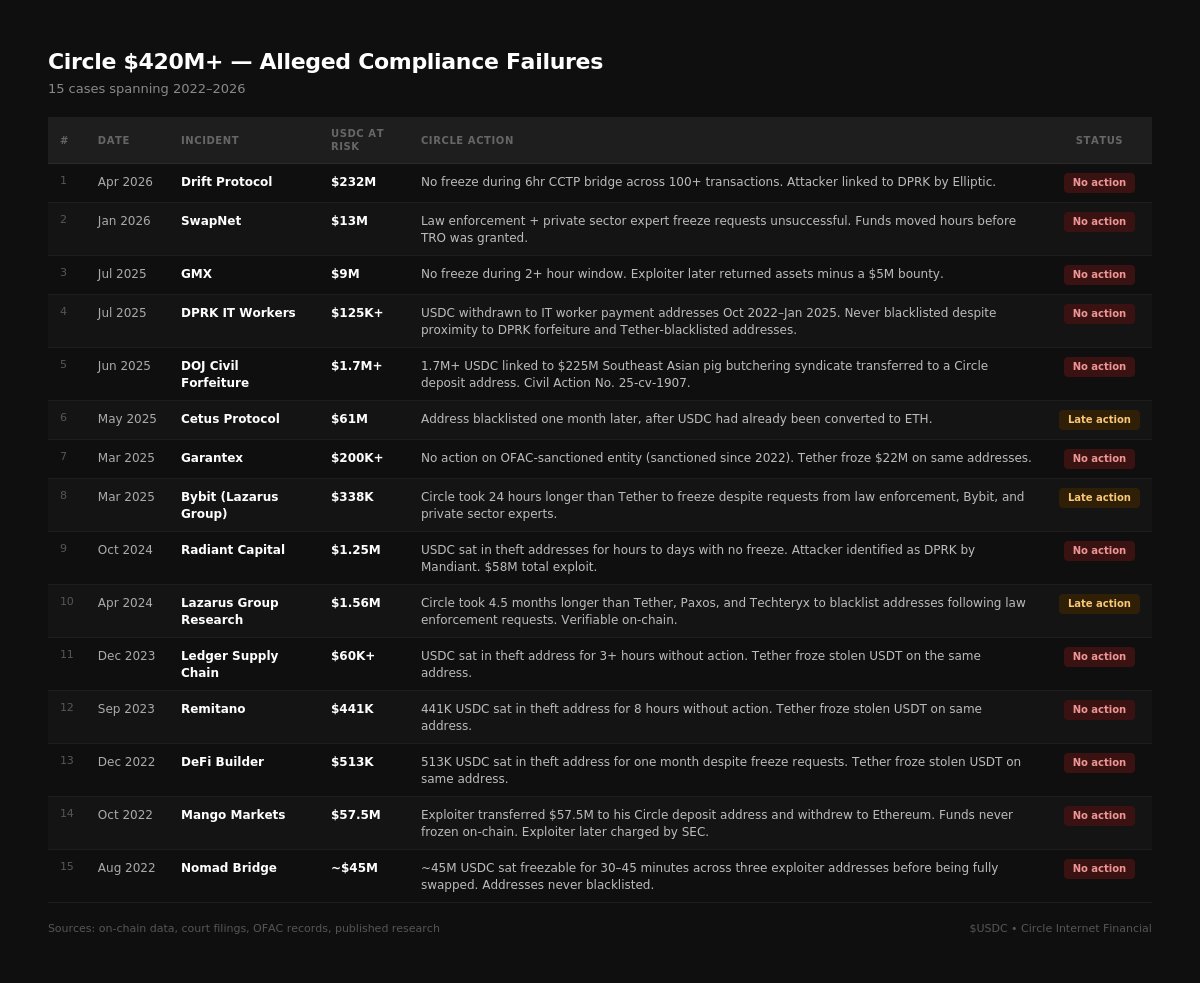
$420M+ in alleged compliance failures since 2022, including fifteen cases of the US-regulated stablecoin issuer taking minimal action against illicit funds.
2/ Circle operates USDC, a centralized stablecoin pegged 1:1 to USD, marketed as a regulated company with a robust compliance program.
Its token contract includes a freeze/blacklist function, and its terms of service explicitly state it reserves the right to restrict access for suspected illicit actors "in its sole discretion".
The company is incorporated in the US, currently headquartered in New York City, and subject to US federal / state financial regulations.
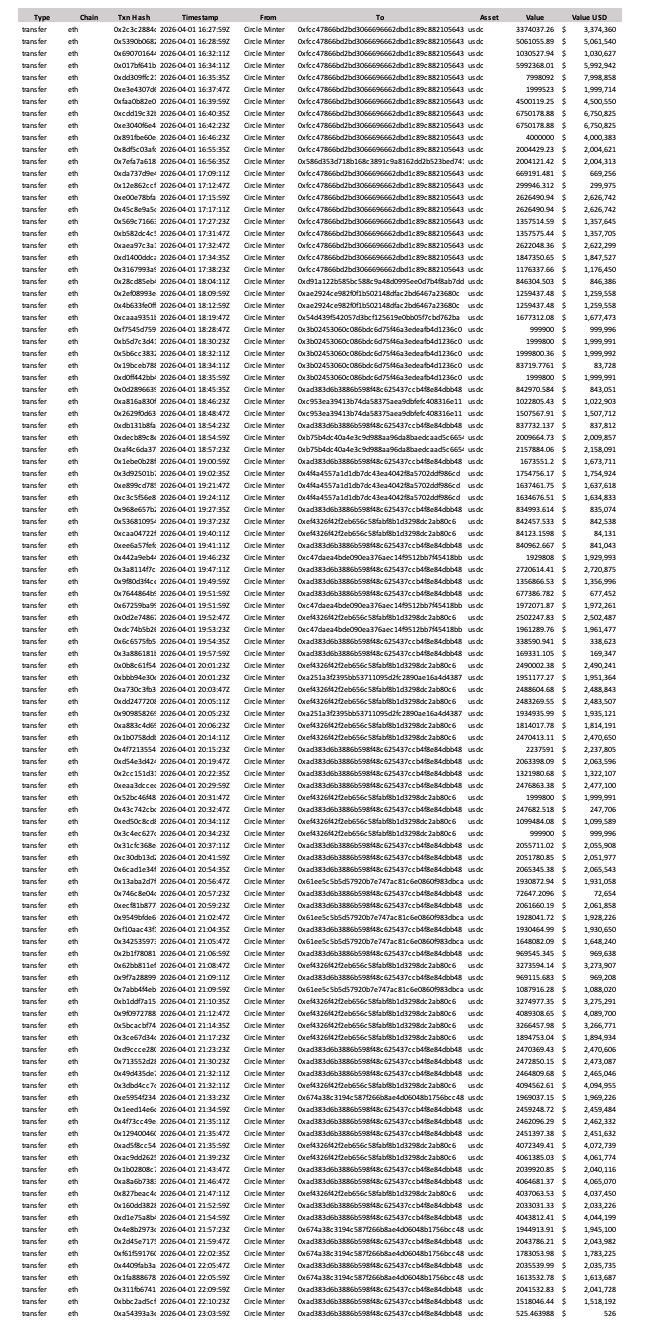
3/ On April 1, 2026, Drift Protocol was exploited for $280M.
The exploiter used CCTP to bridge 232M+ USDC from Solana to Ethereum across 100+ transactions over six consecutive hours. 10+ additional DeFi protocols across the Solana ecosystem were indirectly impacted.
Despite the attacker laundering funds over six consecutive hours across Circle's own native bridge, no USDC was frozen.
The attacker has been linked to DPRK by Elliptic.
Theft address:
HkGz4KmoZ7Zmk7HN6ndJ31UJ1qZ2qgwQxgVqQwovpZES
Update: $230M+ USDC bridged via CCTP from Solana to Ethereum across 100+ txns.
6 hours is how long Circle had to freeze stolen funds from the $280M+ Drift hack.
Circle is a centralized stablecoin issuer headquartered in New York and the attack began around 12 pm ET.
Why does our industry allow them to stay silent?
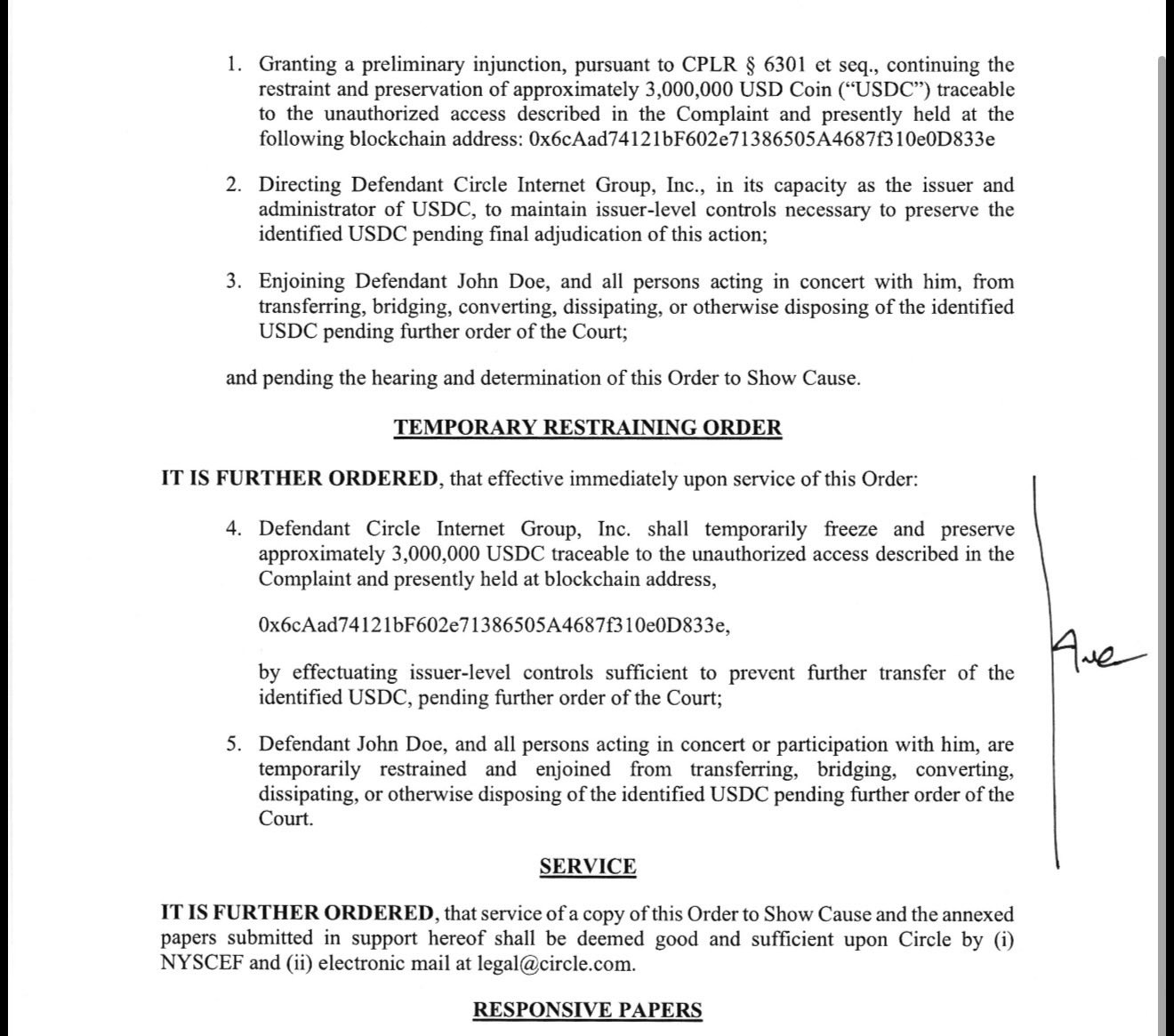
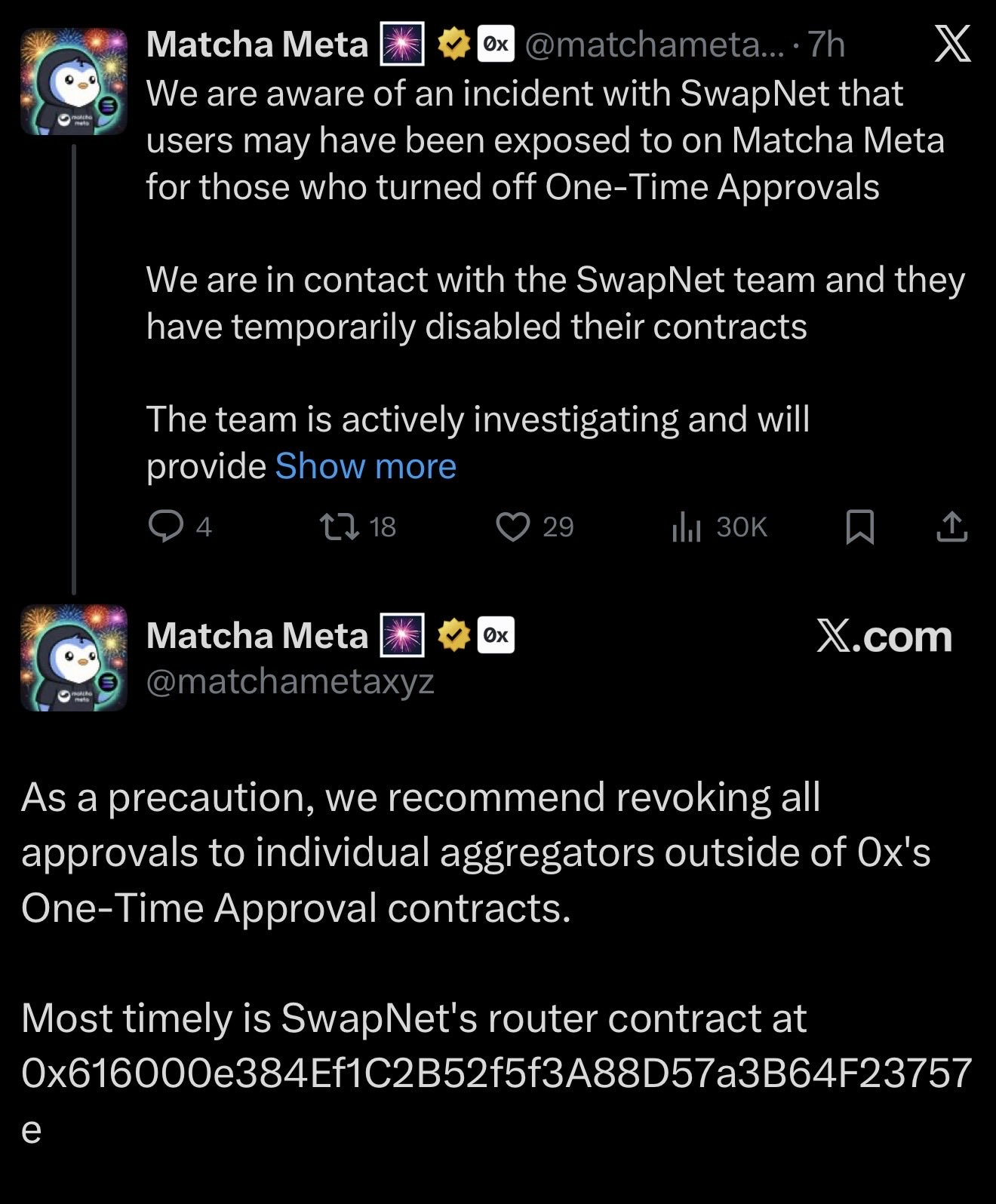
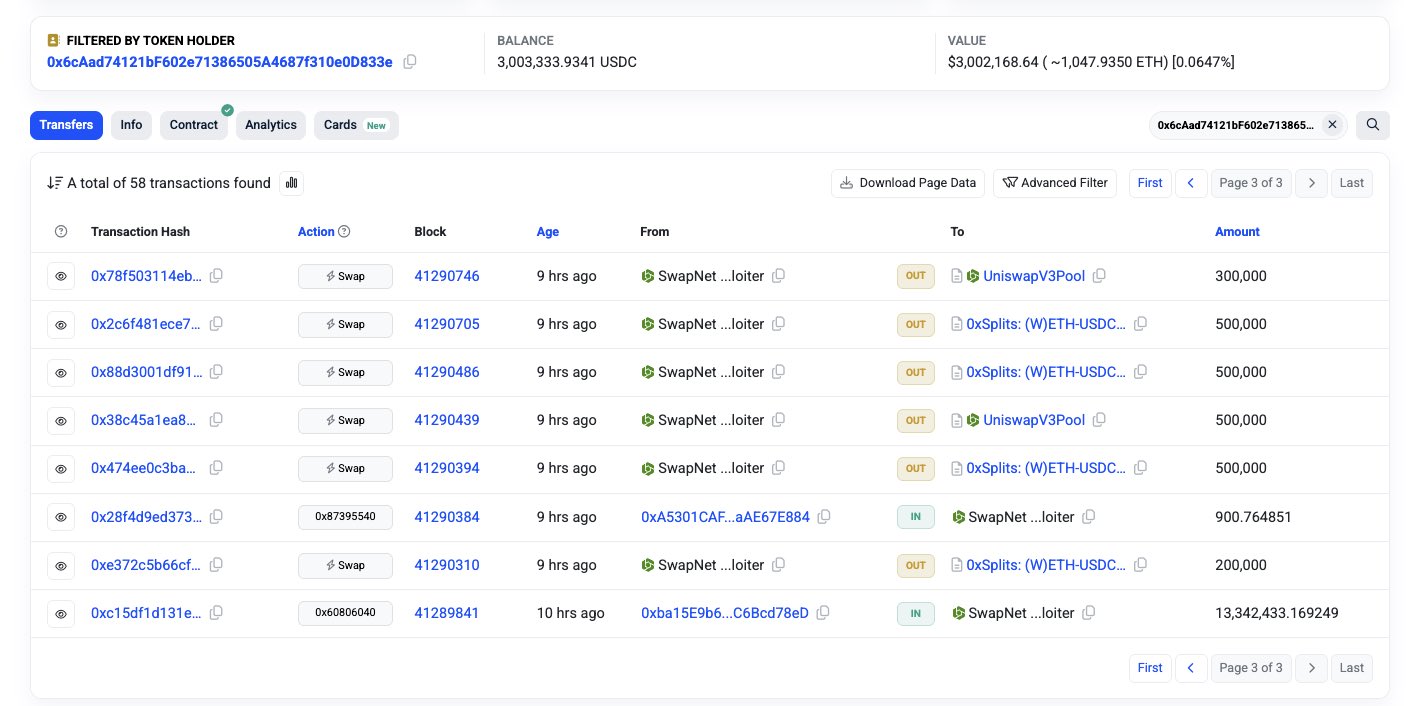
4/ On January 25, 2026, SwapNet was exploited for $16M. 3M USDC sat in the exploiter's address for two days.
Both law enforcement and private sector experts submitted temporary freeze requests to Circle for the theft address. Both were unsuccessful.
One victim pursued a New York court order. The funds were swapped hours before the TRO was granted.
Theft address:
0x6cAad74121bF602e71386505A4687f310e0D833e
History has shown that Circle is a bad actor.
SwapNet contracts were exploited for $13M USDC on Base ~10 hours ago.
3M USDC is still sitting freezable at
0x6cAad74121bF602e71386505A4687f310e0D833e
Why should anyone continue building on $USDC when you never take care of your users as a centralized stablecoin issuer?
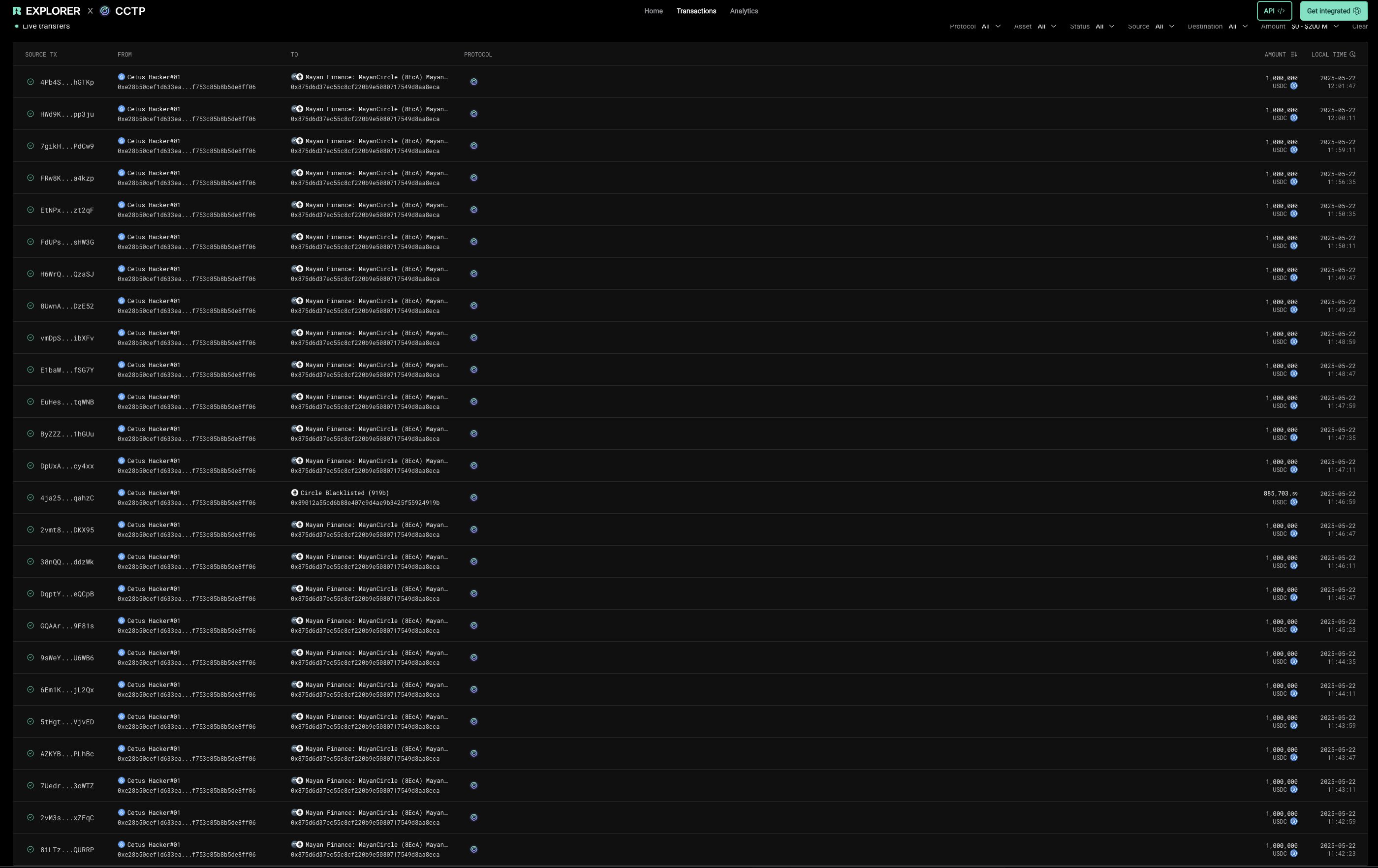
5/ On May 22, 2025, Cetus Protocol was exploited for $223M.
The exploiter used CCTP to bridge 61M USDC from Sui to Ethereum across 60+ transactions over 1.5 hours.
Both the Cetus team and private sector experts requested Circle to freeze the theft address. Circle blacklisted the address one month later, after the USDC had already been converted to ETH.
Theft addresses:
0xe28b50cef1d633ea43d3296a3f6b67ff0312a5f1a99f0af753c85b8b5de8ff06
0x89012a55cD6b88e407C9d4ae9B3425F55924919b
🚨ANNOUNCEMENT
As of earlier today, we have confirmed that an attacker has stolen approximately $223M from Cetus Protocol. We have took immediate action to lock our contract preventing further theft of funds.
$162M of the compromised funds have been successfully paused. We are working with the Sui Foundation and other ecosystem members right now on next-step solutions, with the goal of recovering the remaining stolen funds.
The majority of impacted funds are paused and we are actively pursuing paths to recover the remainder. We have no higher priority and will provide further updates as they become available through this channel. A full incident report will be disclosed later. We are sincerely grateful for your patience. 🙏
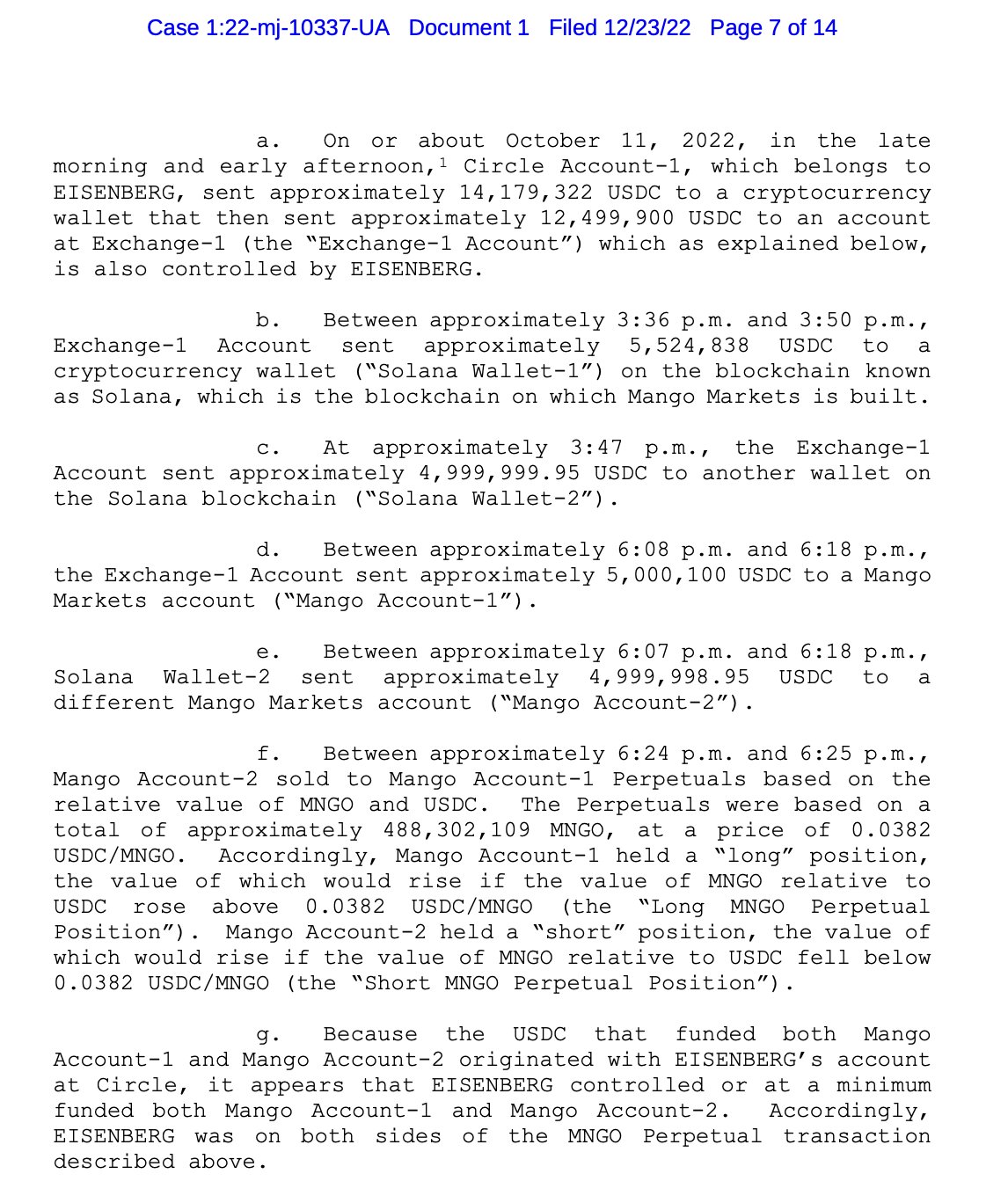
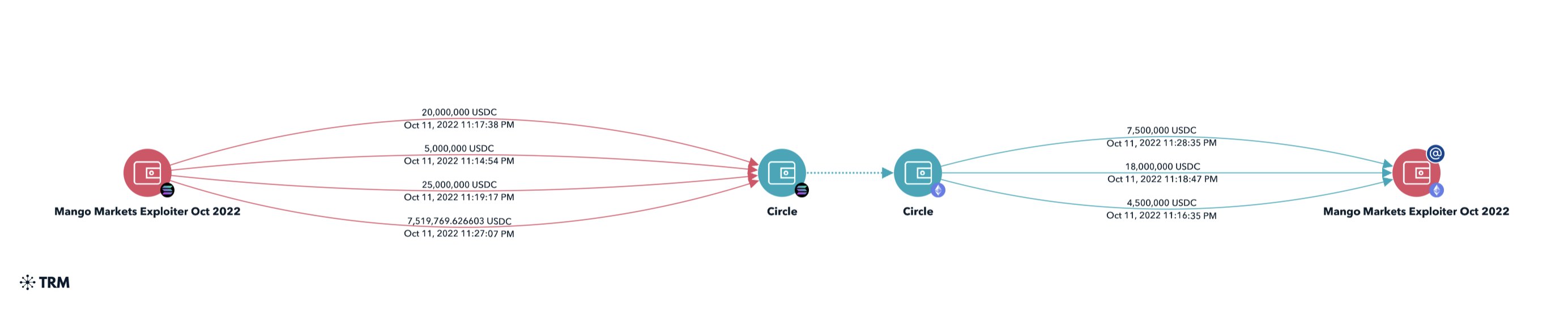
6/ In October 2022 Mango Markets was exploited for $110M.
The exploiter transferred $57.5M to his Circle deposit address on Solana and withdrew the funds to Ethereum. He was later charged by the SEC.
Despite the connection the funds were never frozen onchain.
Theft address
yUJw9a2PyoqKkH47i4yEGf4WXomSHMiK7Lp29Xs2NqM
We are currently investigating an incident where a hacker was able to drain funds from Mango via an oracle price manipulation.
We are taking steps to have third parties freeze funds in flight. 1/
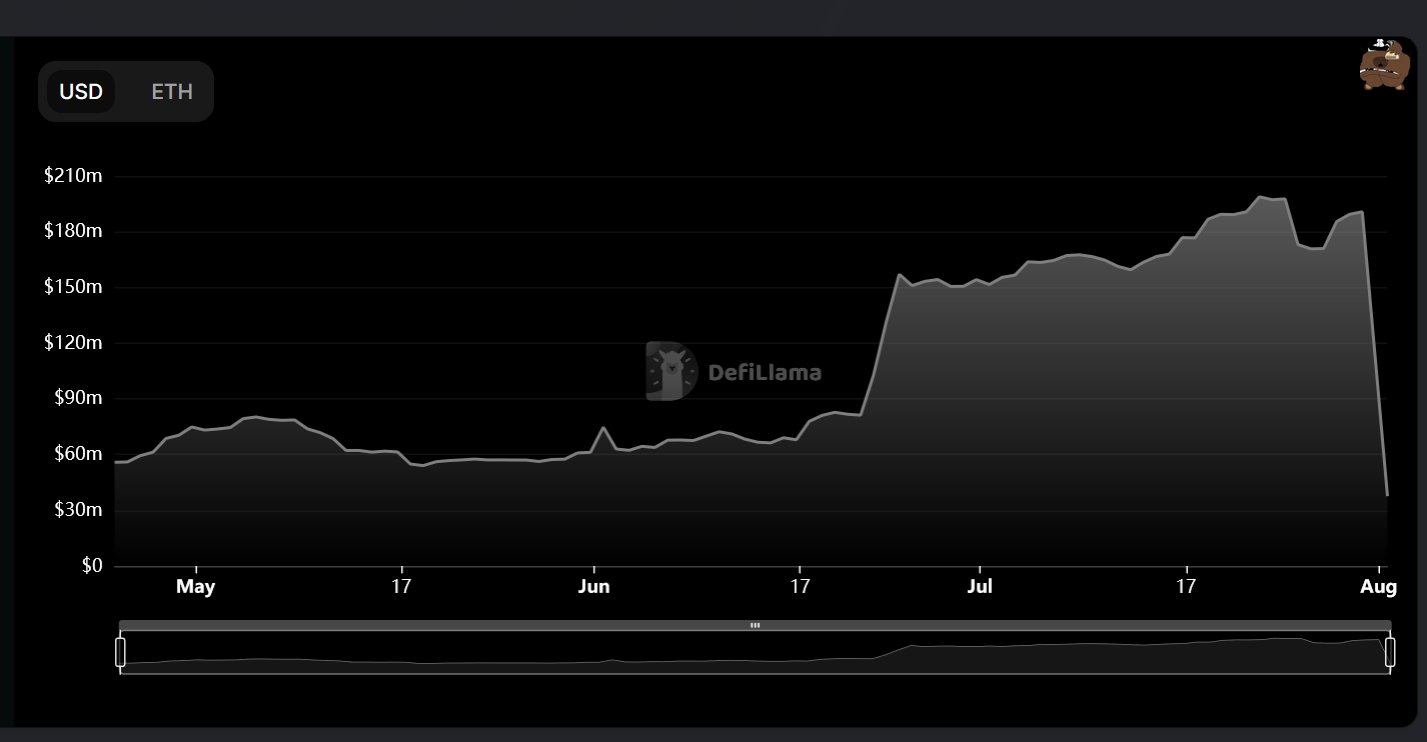
7/ In August 2022 Nomad Bridge was exploited for $190M.
~45M USDC sat freezable for 30-45 min in three exploiter addresses before being fully swapped out.
Despite the large hack being widely reported, the addresses were never blacklisted by Circle.
Theft addresses
0xbf293d5138a2a1ba407b43672643434c43827179
0x56d8b635a7c88fd1104d23d632af40c1c3aac4e3
0xb5c55f76f90cc528b2609109ca14d8d84593590e
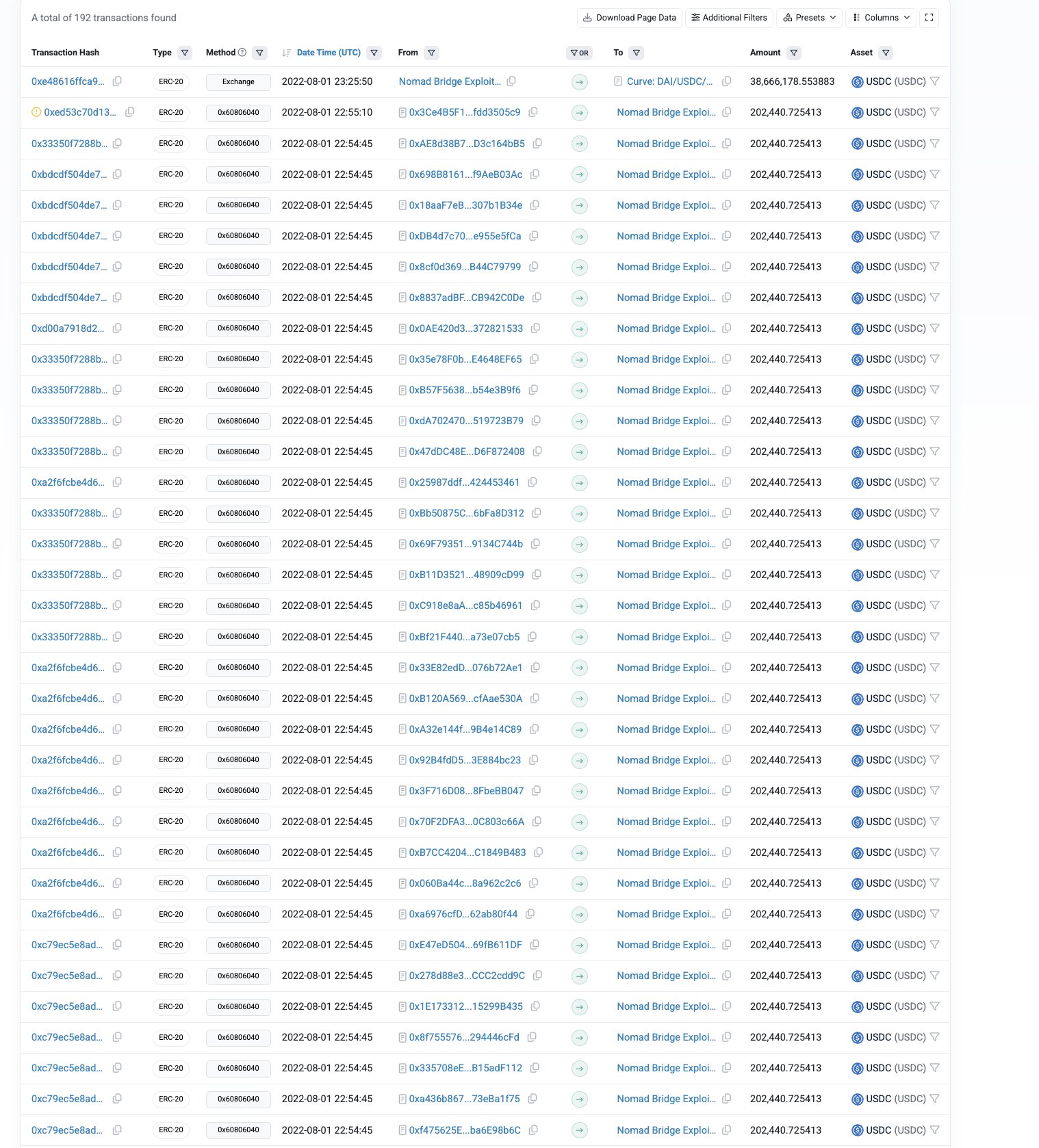

1/ Nomad just got drained for over $150M in one of the most chaotic hacks that Web3 has ever seen. How exactly did this happen, and what was the root cause? Allow me to take you behind the scenes 👇
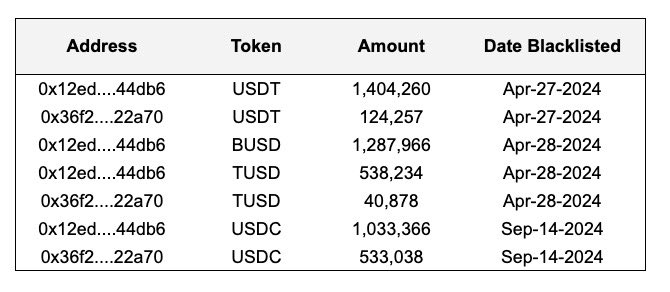
8/ In April 2024 I published a report on Lazarus Group detailing how funds from 25+ hacks were laundered and converted to fiat.
Law enforcement submitted freeze requests to four stablecoin issuers: Circle, Tether, Paxos, and Techteryx for two addresses in relation to the report.
The other three issuers acted promptly. Circle took 4.5 months longer to freeze both addresses (verifiable onchain).
Update: As of today all four stablecoin issuers (Paxos, Tether, Techteryx, Circle) have now blacklisted the two addresses below with $4.96M from Lazarus Group.
0x36f2D3871edd59d5C06DB8F0b12bE928d5922A70
0x12ED7f6ed0491678764c2b222A58452926E44DB6
Another $1.65M is frozen at various exchanges bringing the total frozen from my investigation to $6.98M.
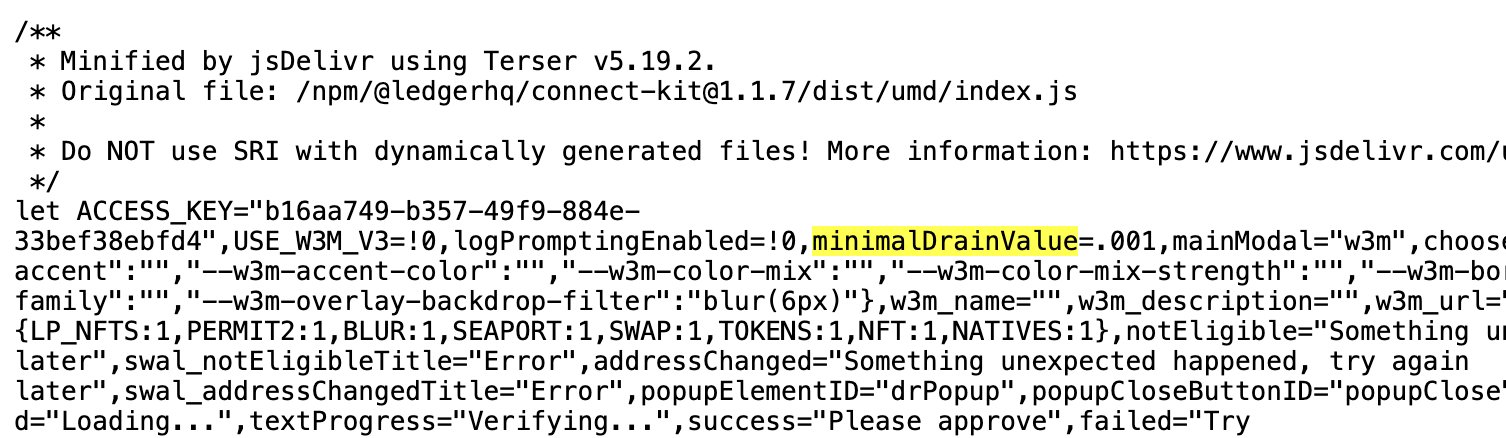
9/ In December 2023 Ledger, the largest hardware wallet company, fell victim to a supply chain attack which resulted in a phishing drainer being added to its Ledger Connect kit and $600K+ in assets stolen.
USDC sat in the theft address for 3+ hours without action from Circle. Tether froze the stolen USDT in the same address.
Theft address:
0x658729879fCa881D9526480B82aE00EFc54B5c2d"
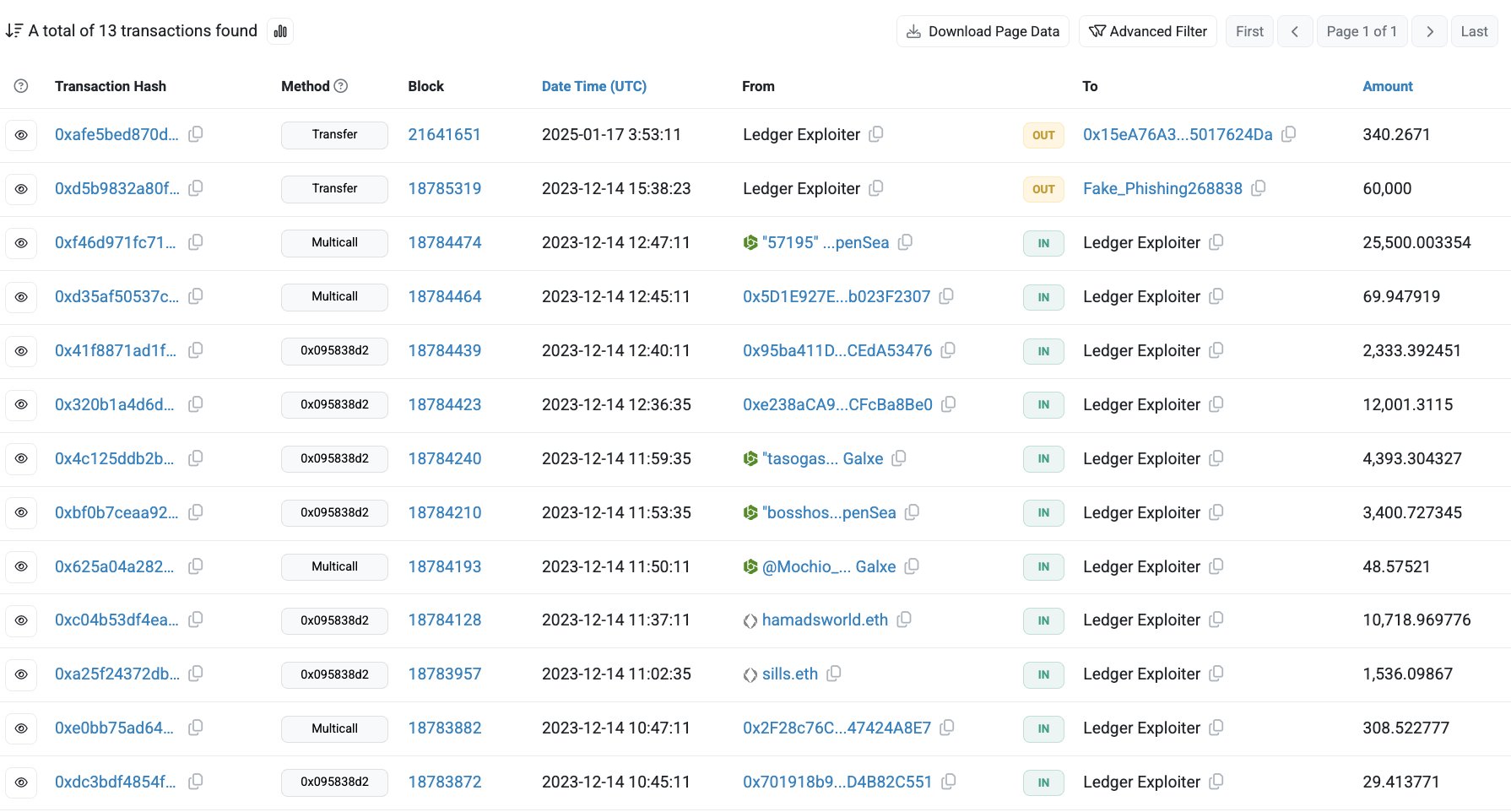
🚨 ledger library confirmed compromised and replaced with a drainer. wait out interacting with any dapps till things become clearer.
cdn.jsdelivr.net/npm/@ledgerh…
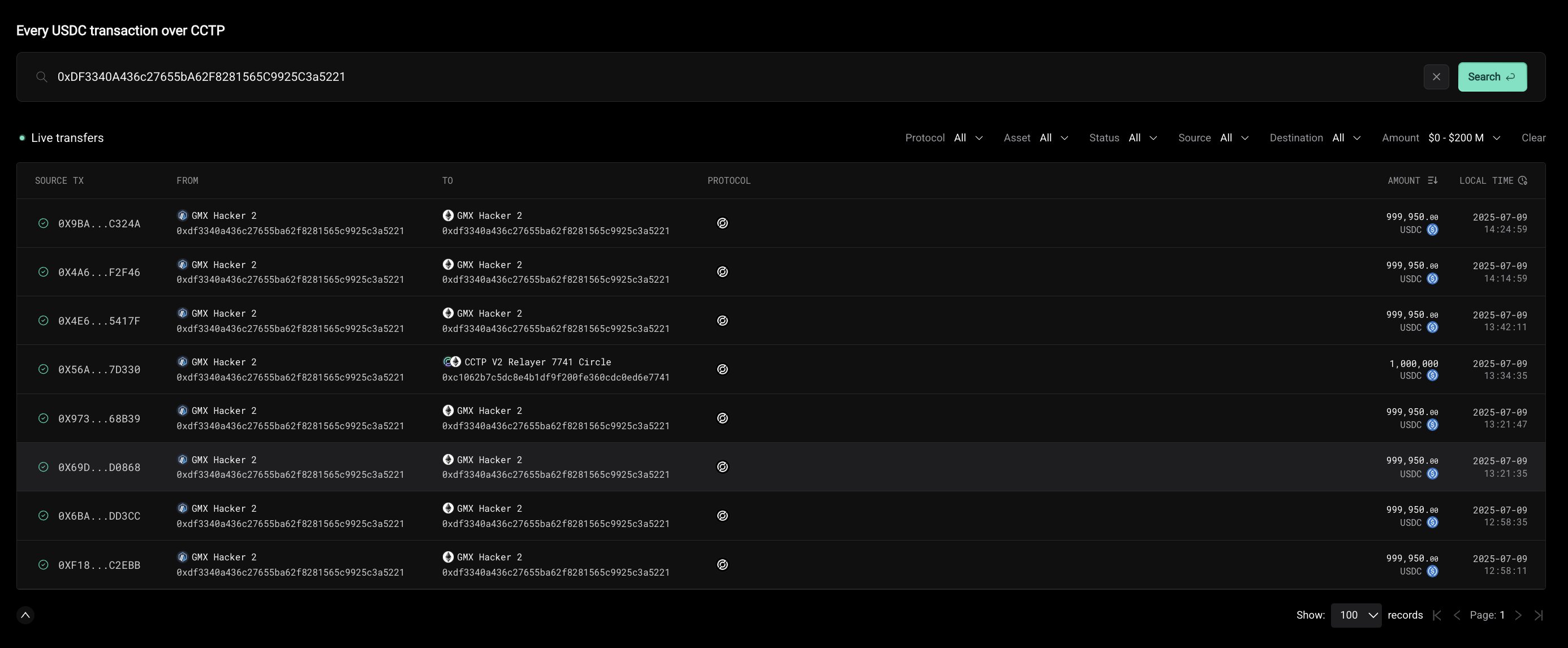
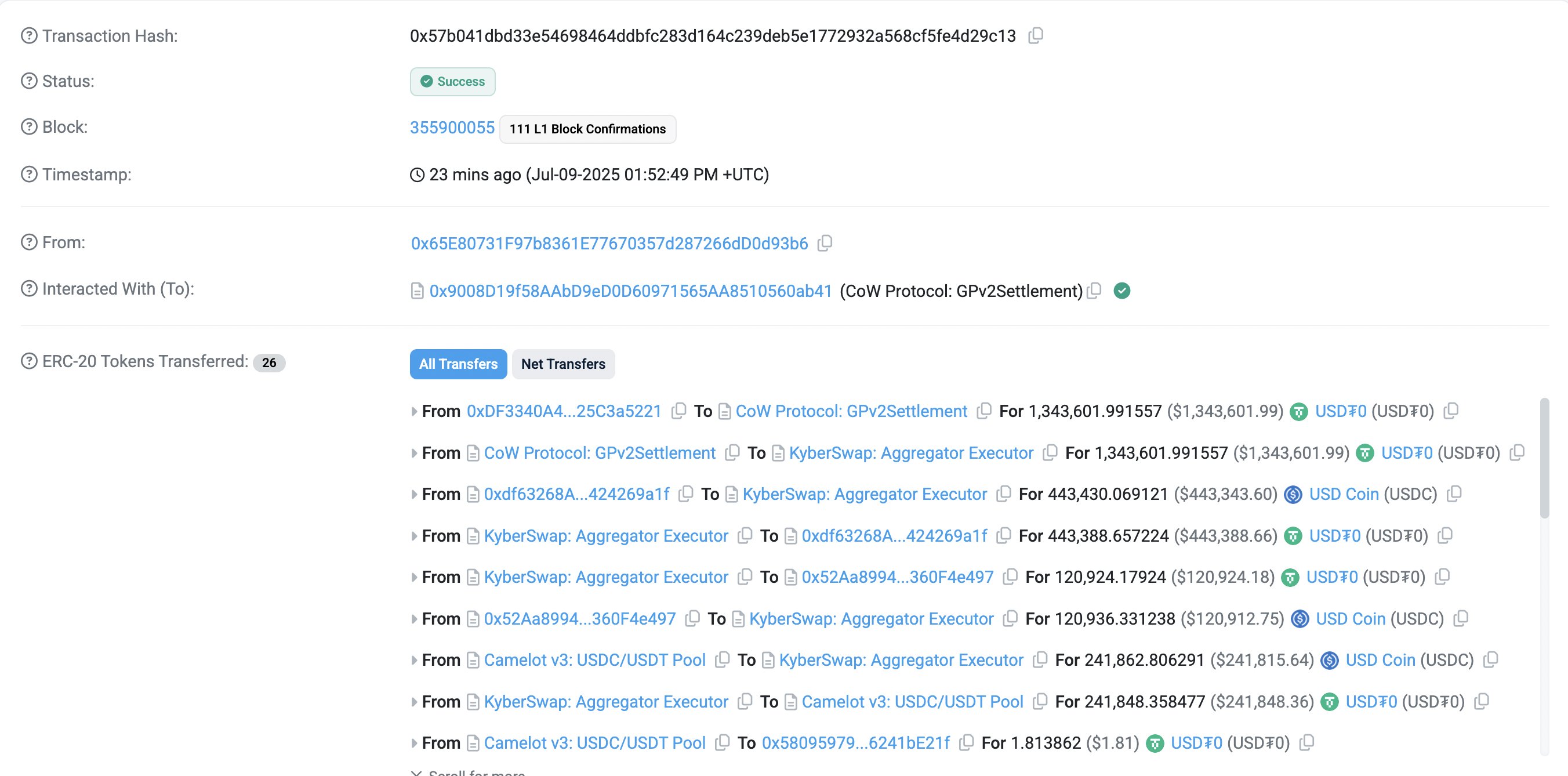
10/ On July 9, 2025 GMX was exploited for $40M.
9M USDC sat for 2+ hours and was partially bridged from Arbitrum to Ethereum via CCTP.
While the exploiter later returned assets minus a $5M bounty, the USDC was not frozen during the 2+ hour window.
Theft address
0xDF3340A436c27655bA62F8281565C9925C3a5221
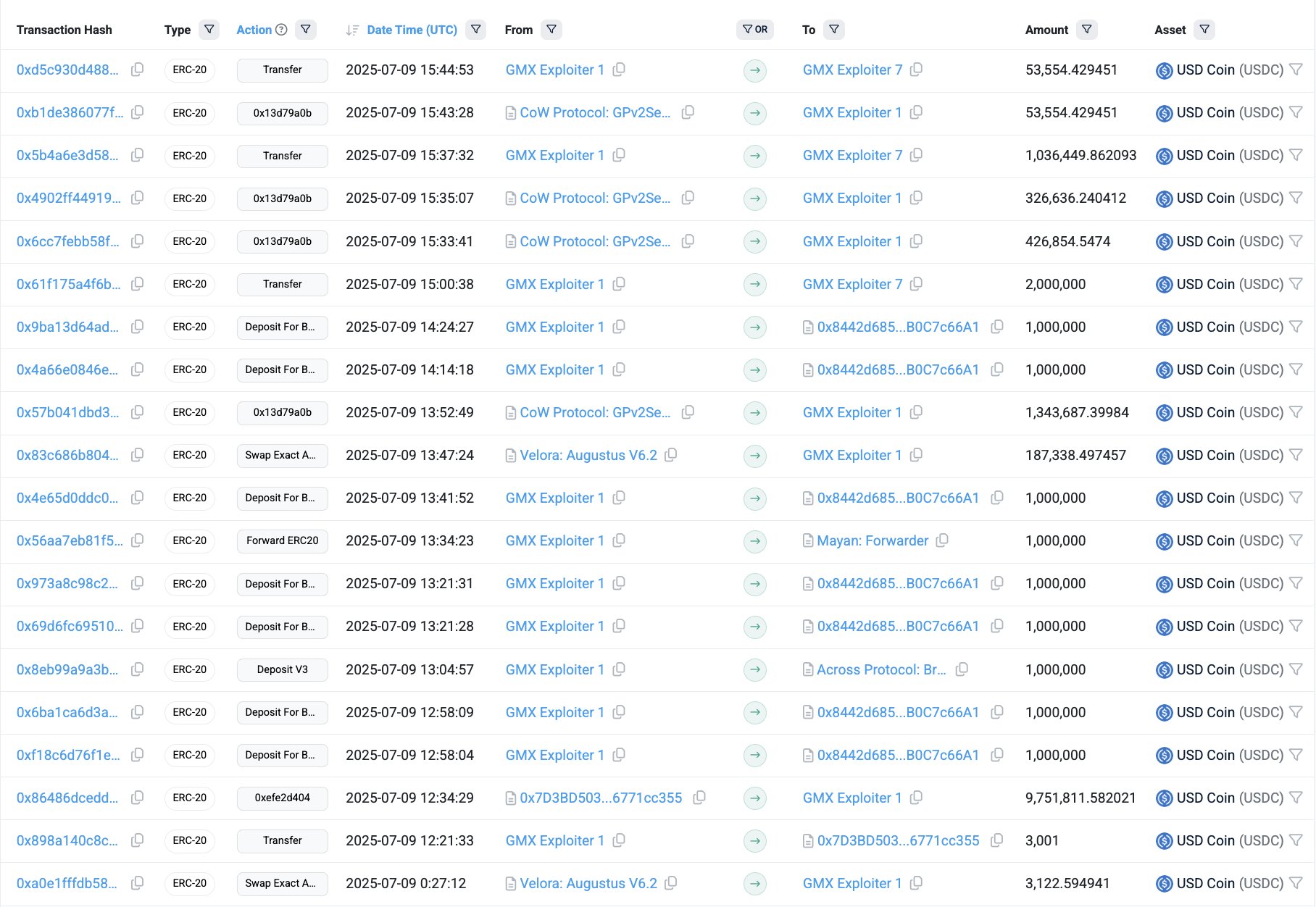
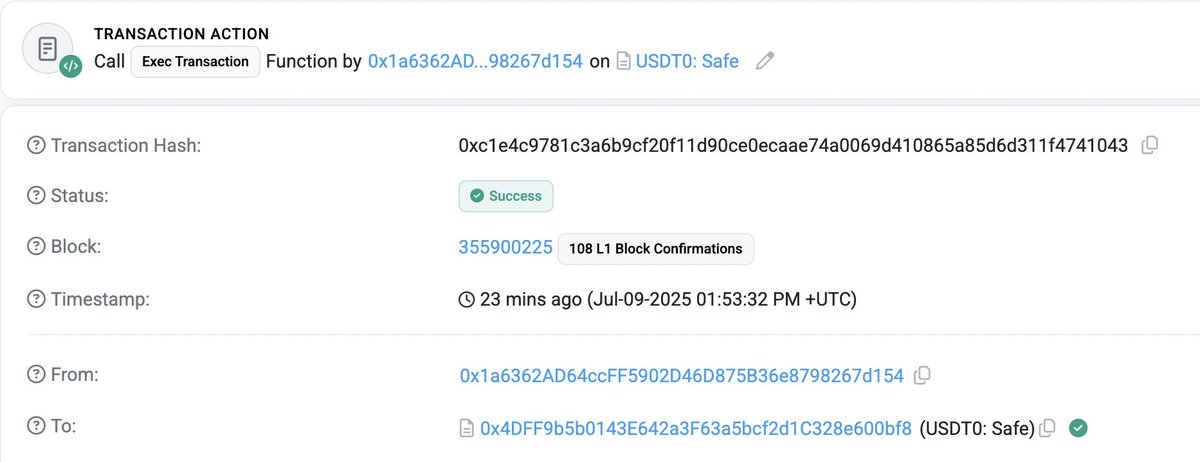
This is absolutely INSANE!
The exploiter held 1.3M USDT0 and the @USDT0_to team immediately froze the address...
However, the attacker managed to swap out all the USDT0 for USDC just 23 seconds before being frozen!
It's been more than an hour since the exploit and @circle still hasn't responded or frozen...
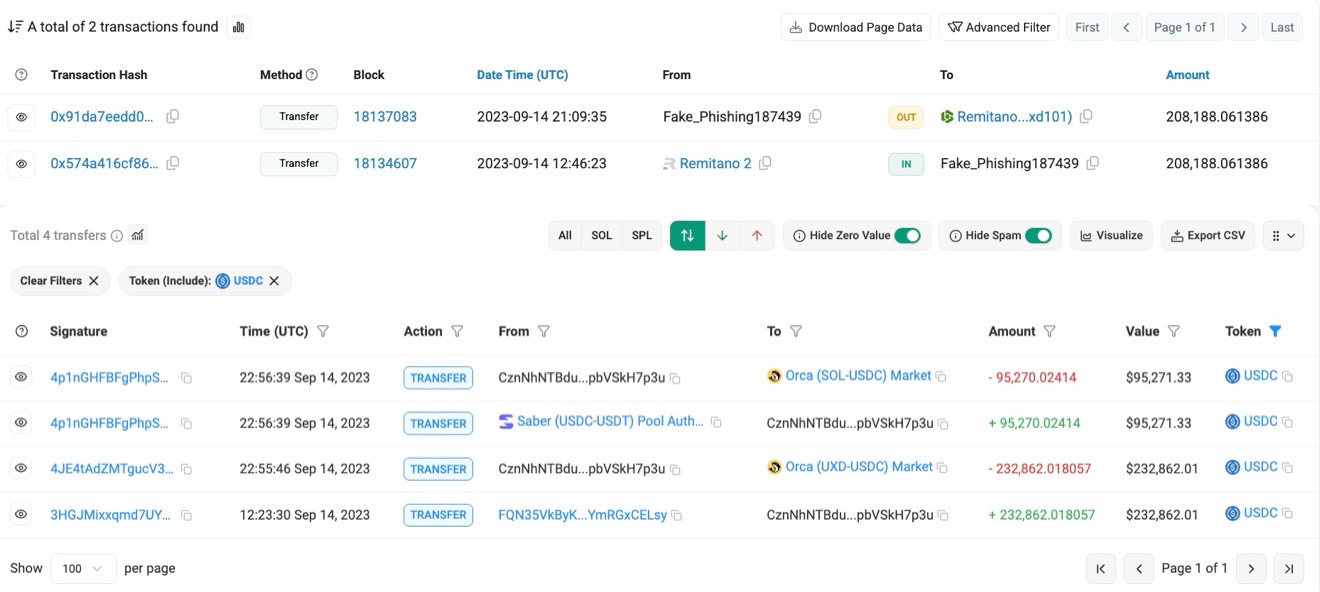
11/ In September 2023 Remitano was hacked for $8.5M from its hot wallets on multiple chains.
441K USDC sat in theft addresses for 8 hours without action from Circle.
Tether froze 1.4M USDT in the same addresses.
Theft addresses
CznNhNTBduDTbAUsFbJrCfLCrgzpyNWZwXpbVSkH7p3u
0x74530e81e9f4715c720b6b237f682cd0e298b66c
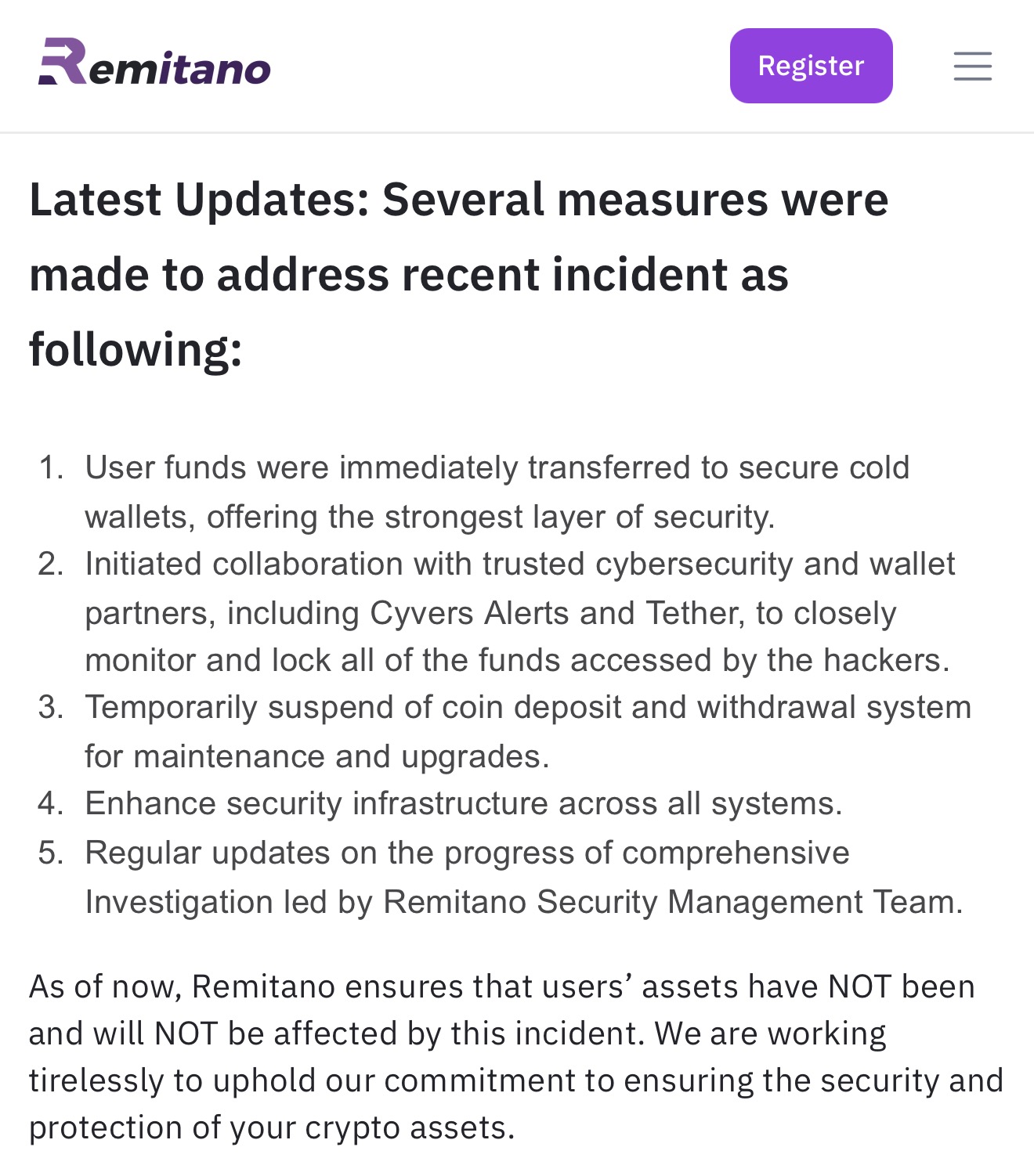
#latestupdates We understand the seriousness of this matter and we want to assure you that Remitano is actively taking steps to address all security concerns and rectify the situation.
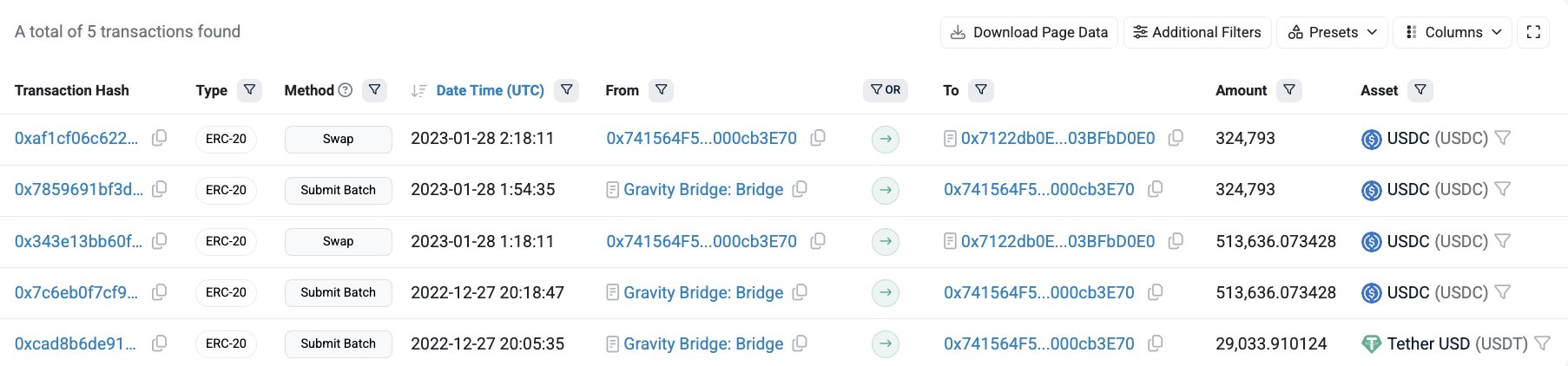
12/ In November 2022 a DeFi builder had ~$20M stolen by a threat actor from multiple wallets on various chains.
513K USDC sat in a theft address for one month and no freeze was executed by Circle while a request was sent out.
Tether froze stolen USDT in the same address.
Theft address
0x741564f5563abbe85f1b091eb39e38c000cb3e70
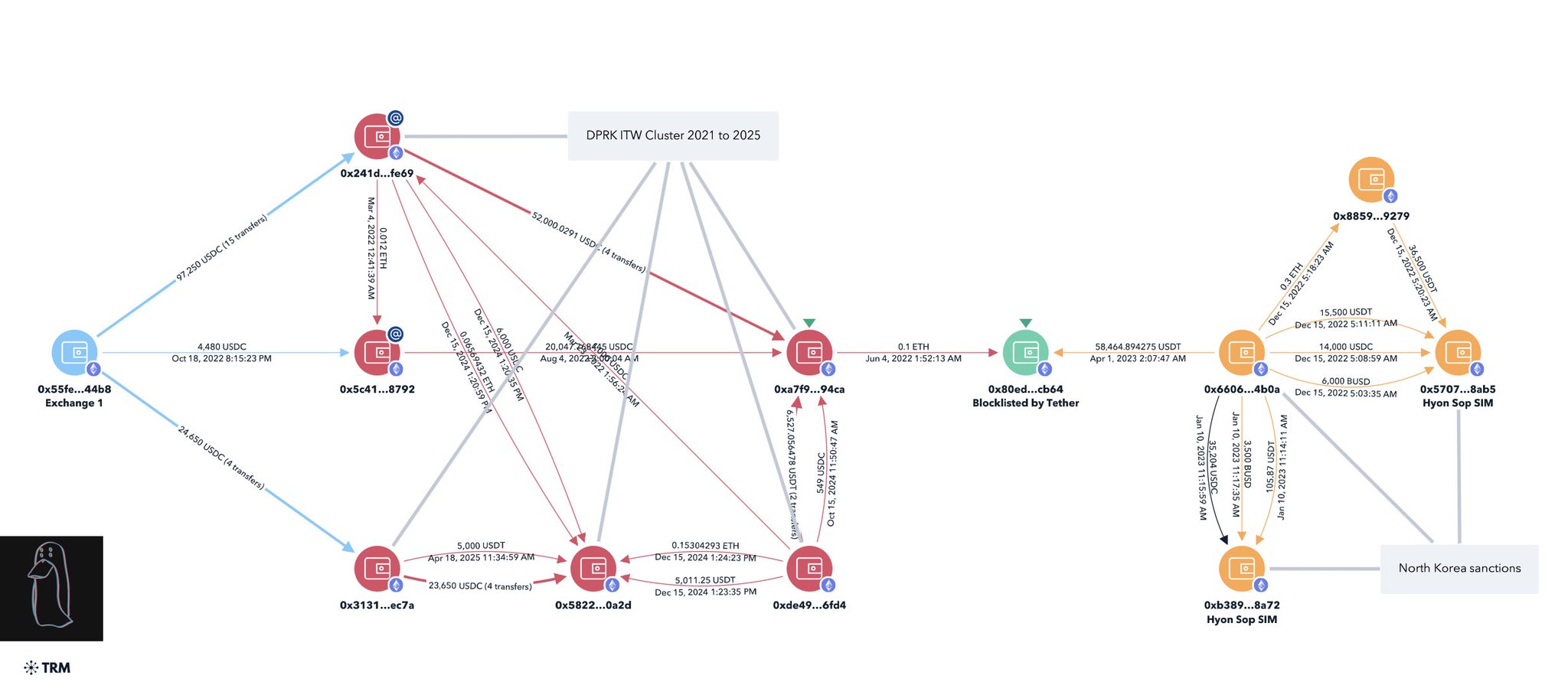
13/ In July 2025 I published research on DPRK IT workers infiltrating crypto businesses.
Between October 2022 and January 2025, Circle users withdrew USDC to three IT worker payment addresses. These addresses were three hops from a DPRK forfeiture address and two hops from an address previously blacklisted by Tether.
The DPRK ITW addresses in the cluster were never blacklisted by Circle.
Circle withdrawal address
0x241d2b20f2c26a2541a0f121d6a33c29cb4cfe69
0x3131f63378cedc21a9c2fdf6574248a8cb7eec7a
0x5c411cb174c2e163f6465252ae895f3e3e5a8792
1/ My recent investigation uncovered more than $16.58M in payments since January 1, 2025 or $2.76M per month has been sent to North Korean IT workers hired as developers at various projects & companies.
To put this in perspective payments range from $3K-8K per month meaning they have infiltrated 345 jobs on the low end or 920 jobs on the high end.

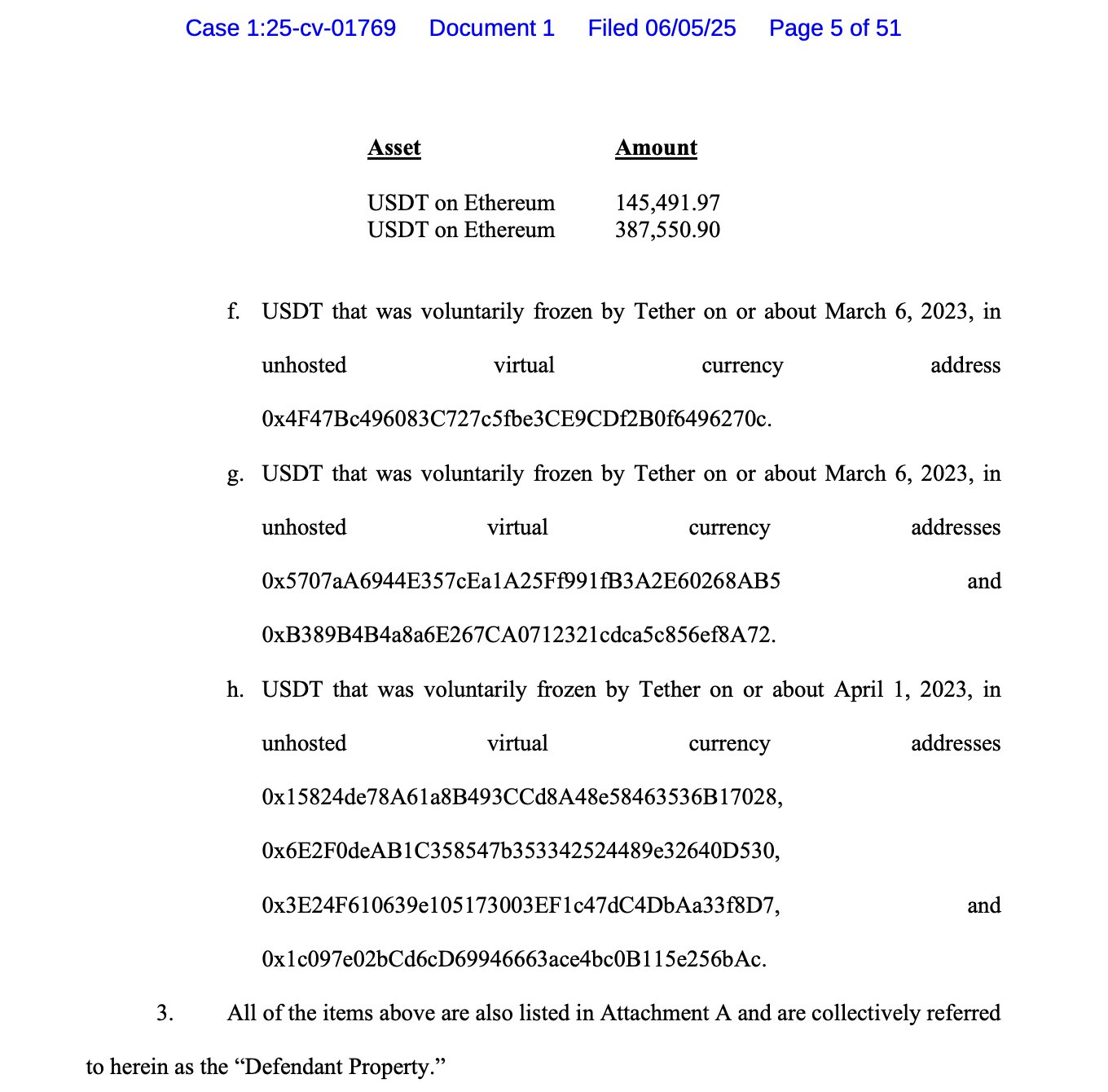
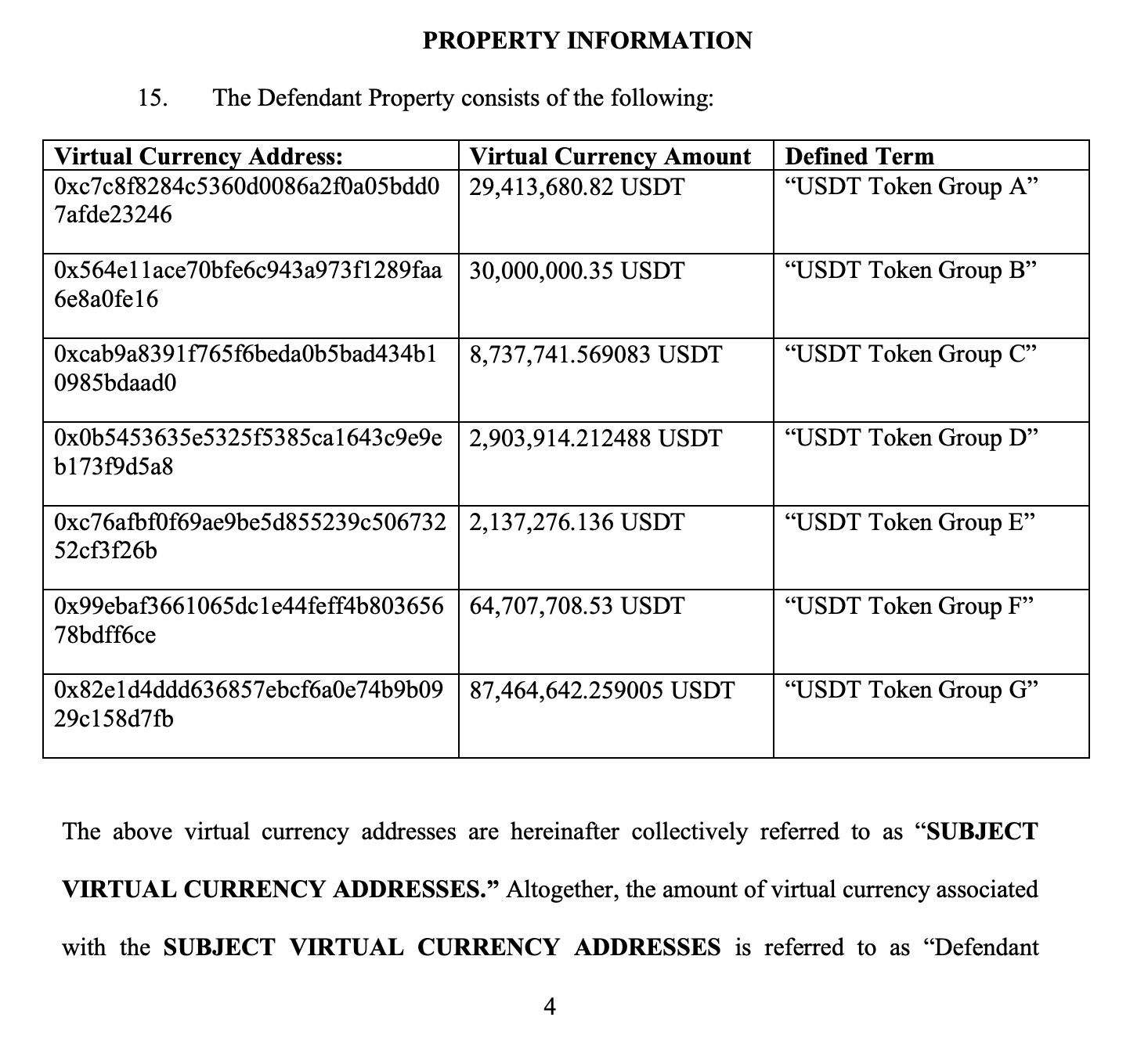
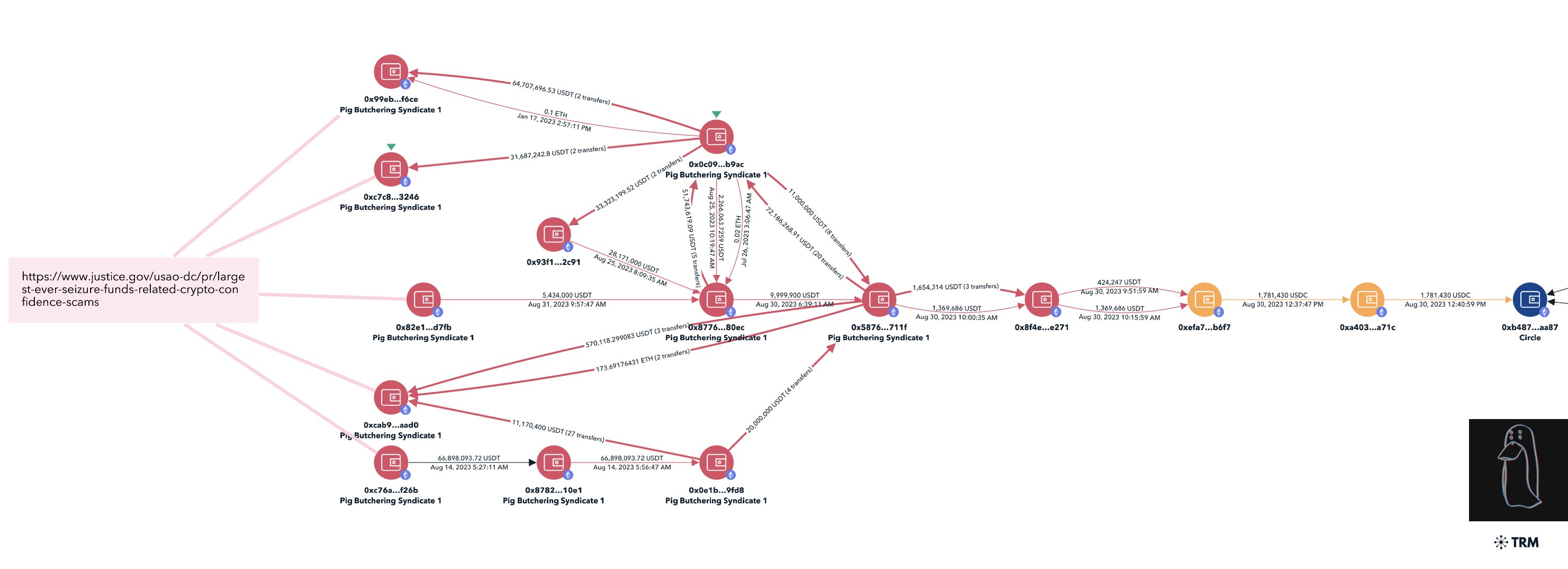
14/ In June 2025 a US DOJ civil forfeiture complaint was filed in relation to a $225M USDT seizure linked to a Southeast Asian pig butchering syndicate.
1.7M+ USDC linked to the illicit funds was transferred through intermediary addresses to a Circle deposit address.
Circle deposit address:
0xb4875c44fa2b00291637793196f077b197daaa87
Civil Action No. 25-cv-1907

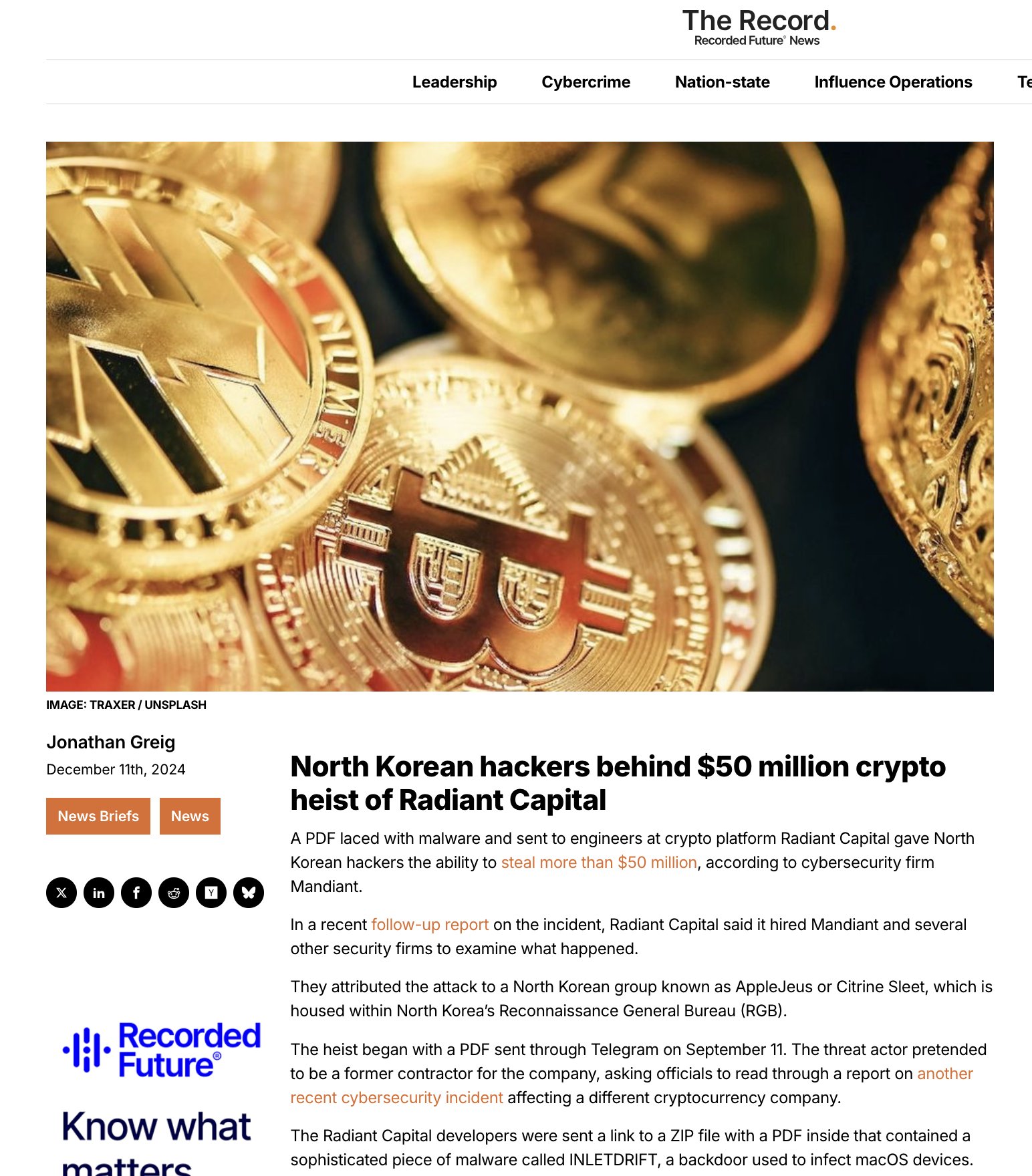
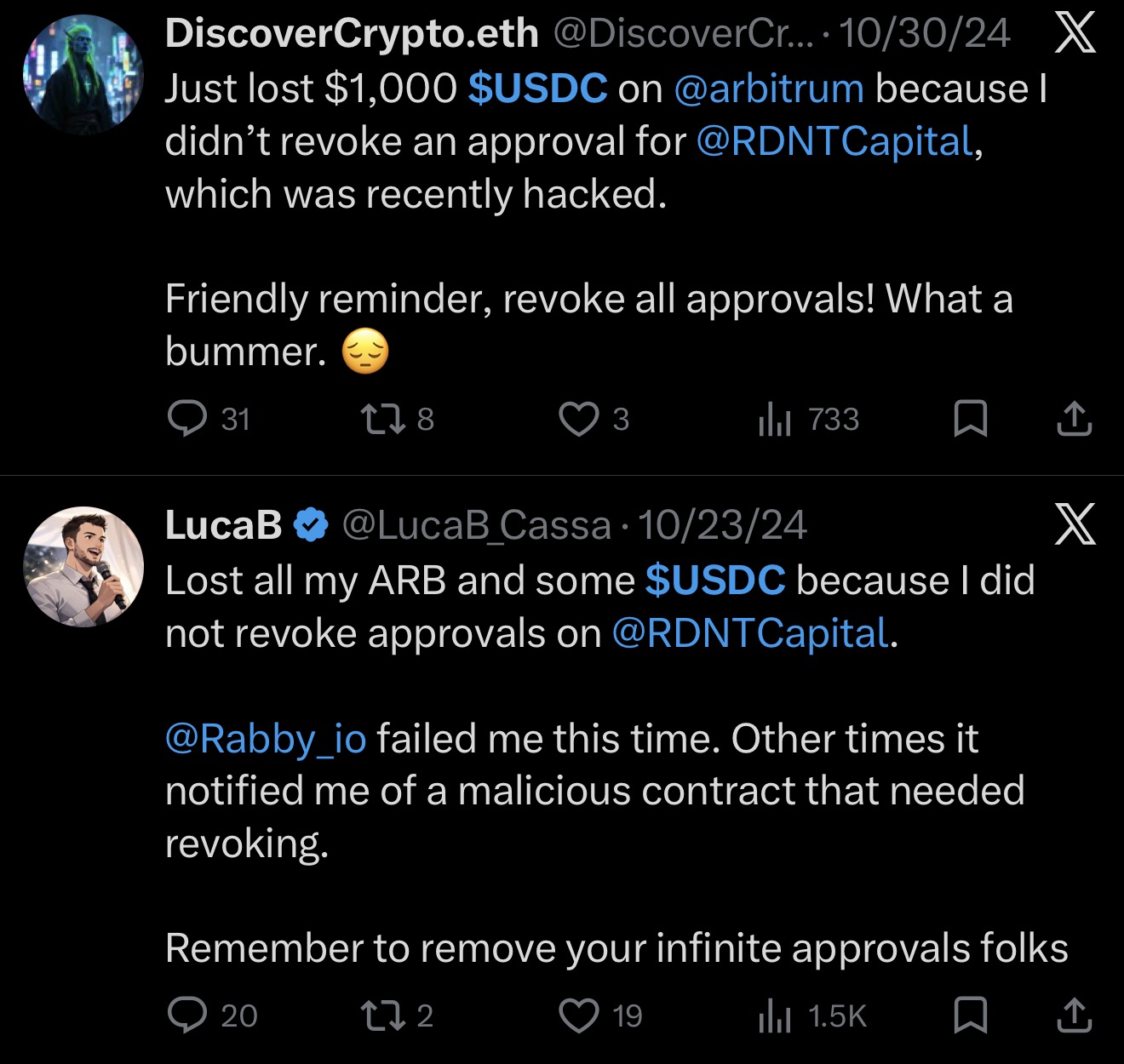
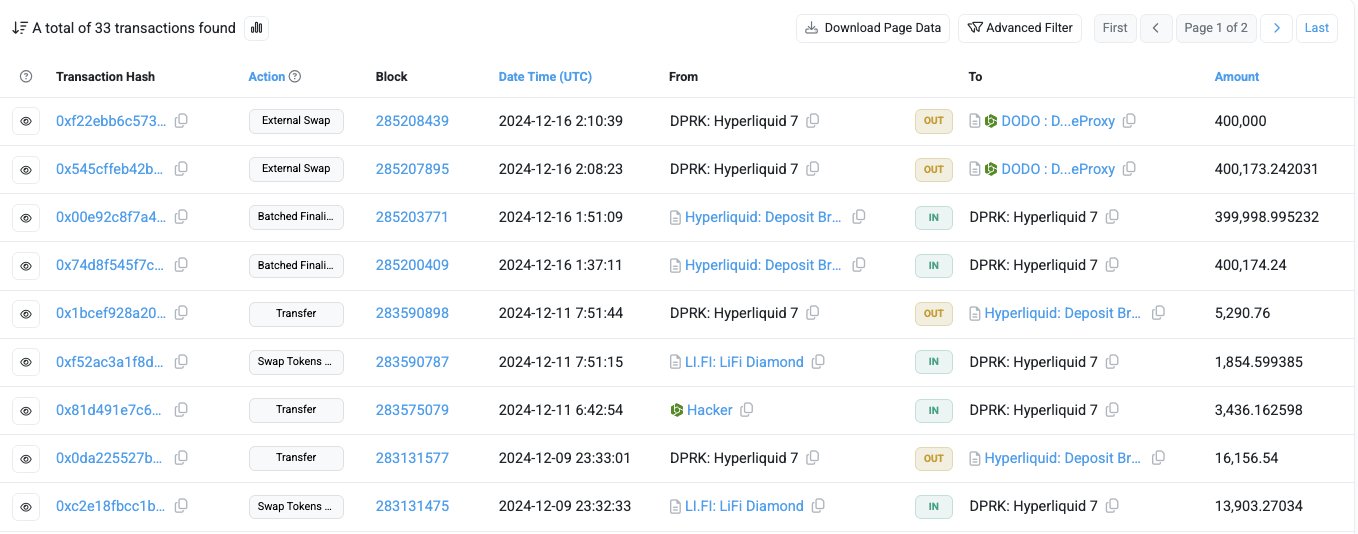
15/ In October 2024 Radiant Capital was hacked by Lazarus Group (Apple Jeus) for $58M.
The attacker drained USDC from victims via open approvals and chainhopped from Hyperliquid to Arbitrum using USDC.
Multiple instances had USDC sitting in theft addresses for hours with no freeze action from Circle.
Theft addresses
0x52263cAEc2e144C3A84cc16d014157360Ac85A89
0x00E1559184Bf1da0256a495ae9BAec11BCA60eb7
0x7997e80F4bD9563d61EE4D06108f7D6cEB23Ab21
0x60ABA279E49E5A05DC7e3c84F2204a6Afb032119
0x5b10daEdC2D7B5CE47f6B3072188f758f1b14481
0x34aa91e574aa963675107011DcF0392C5521005a
0x348FC4DfdCD3427D8A4B43Ad965B4443d55CF955
We are aware of an issue with the Radiant Lending markets on Binance Chain and Arbitrum. We are working with SEAL911, Hypernative, ZeroShadow & Chainalysis and will provide an update as soon as possible. Markets on Base and Mainnet are paused until further notice.
16/ In March 2025 law enforcement from multiple jurisdictions seized Garantex infrastructure. Garantex had been OFAC sanctioned since 2022.
Tether froze $22M in connected addresses. Circle took no action on 200K+ USDC in the same addresses.
Garantex address:
0xb271036d95b205a26bae5cb2d4eb922c000903a2"
Garantex is an OFAC sanctioned entity and just had infra taken down, assets seized, team members charged by law enforcement from multiple countries (US, Germany, Finland)
They were used to launder hundreds of millions from ransomeware, DPRK hacks, etc
22.8M+ USDT was blacklisted the other day
Why has Circle still not blacklisted even though a few Garantex addresses hold USDC?
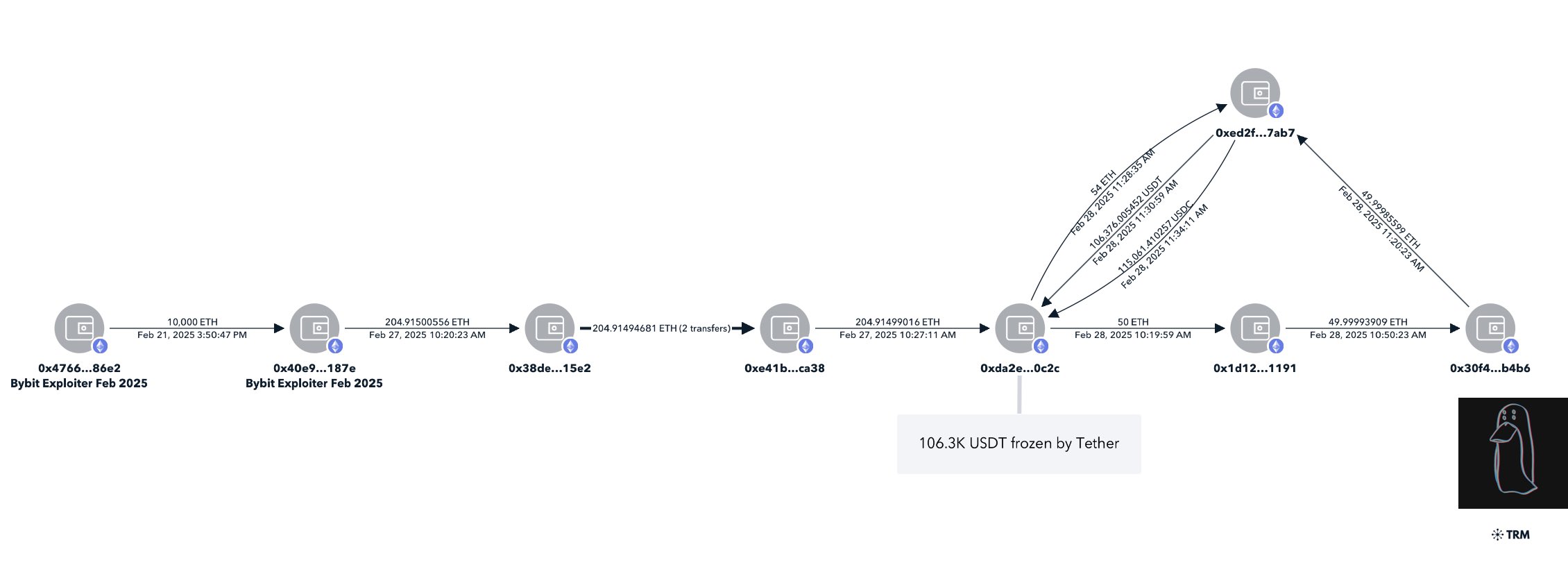
17/ On February 21, 2025, Bybit was hacked by Lazarus Group for $1.5B, widely reported across mainstream media.
On February 28, 106K USDT and 338K USDC consolidated to theft address 0xDa2.
Law enforcement, Bybit, and private sector experts submitted freeze requests to both Tether and Circle.
Tether froze the address within hours. Circle took 24 hours longer to act.
Theft address:
0xDa2e12E94060720581994eEc870F83d9C7200c2c
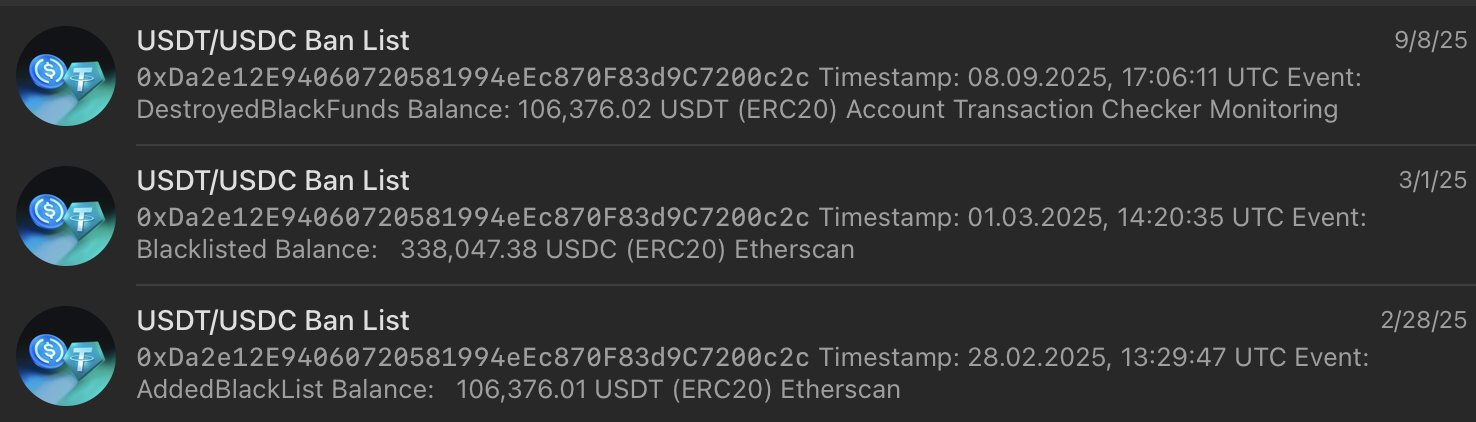
How about you tell the entire community why Circle has yet to freeze 115K USDC directly tied to the Bybit hack by DPRK with zero obfuscation after 5 hours?
Meanwhile Tether already froze 106K USDT multiple hours ago.
How many more examples will people have to show until the space understands Circle is a bad actor.
0xDa2e12E94060720581994eEc870F83d9C7200c2c
18/ Circle builds good products and I hold USDC myself. This isn't a post about hoping they collapse.
But the decisions they've made around compliance have had real consequences for real people.
Nine figures lost from the ecosystem because of repeated inaction across three years, law enforcement requests, private sector requests, and their own infrastructure.
The $420M+ figure only accounts for major public cases. The real figure is likely significantly higher.
They have every tool and resource available to do better. They just haven't.
So I'll leave you with one question: who is Circle actually serving?
A US-regulated public company owes it to its users and the broader community to do better than this.