Security Update: Token Gateway exploit
On April 13, 2026, a vulnerability in Hyperbridge’s Token Gateway was exploited, resulting in approximately $237,000 in losses on Ethereum.
Bridging operations were paused immediately after detection, and this is an update on the situation.
🧵
This incident was isolated to only bridged DOT on Ethereum. Hence, native DOT on the Polkadot relay chain, parachains, and other assets across Hyperbridge remain completely secure and unaffected.
Most blockchain bridges rely on validators or multisigs to approve transactions, which introduces human trust assumptions and has led to over $2B in bridge-related losses.
Hence, Hyperbridge was designed to instead use cryptographic proofs generated directly from blockchain state, eliminating trust and reducing attack surfaces. But this exploit didn’t compromise that model.
It stemmed from a vulnerability in the Solidity-based Merkle Mountain Range (MMR) proof verification logic, specifically within the Merkle tree verifier implementation, which was designed to closely mirror upstream Polkadot logic.
Update: Further investigation indicates the root cause is proof forgery due to missing input validation in the VerifyProof() function of @hyperbridge ’s HandlerV1 contract.
Specifically, the verifier does not enforce leaf_index < leafCount. If an attacker submits leafCount = 1 and leaf_index = 1, CalculateRoot() in the MMR path never incorporates the request commitment into root computation, so the proof can pass for arbitrary request content.
This fully decouples the proof from the message it is meant to authenticate, enabling attackers to forge seemingly valid cross-chain messages against any historical overlayRoot.
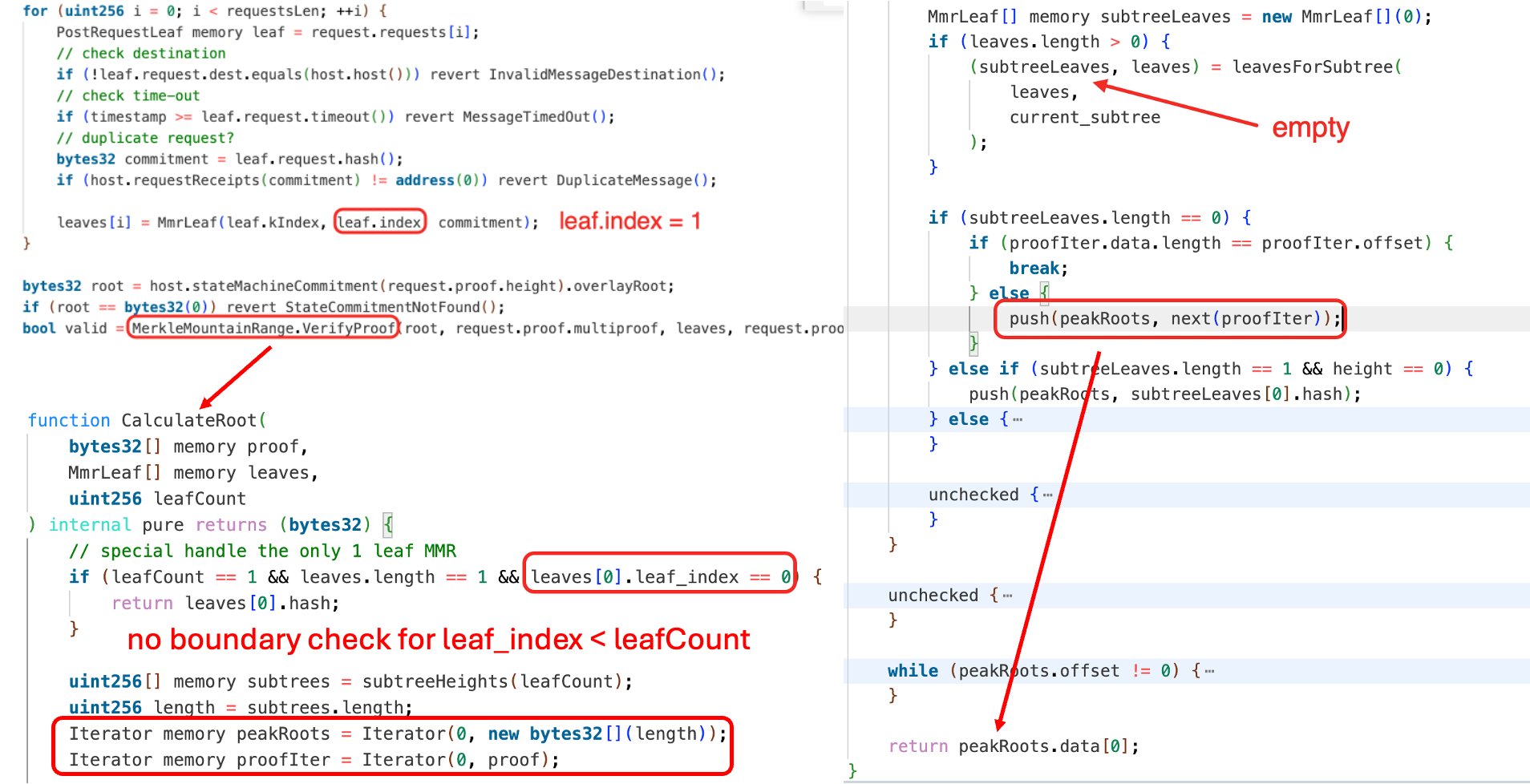
This flaw allowed invalid proofs to be incorrectly accepted as valid.
As a result, a malicious message was processed that granted the attacker administrative control of the bridged DOT token contract on Ethereum.
The attacker minted 1 billion bridged DOT tokens (over 2,800x the legitimate circulating supply (~356K tokens)), and sold them on a decentralized exchange.
We’re actively working with security partners to track and recover the affected funds.
Bridging will remain paused while additional safeguards are implemented and reviewed.
We’ll share further updates as we progress.
For questions or support, please reach out to: ops@polytope.technology