The KelpDAO exploit (~$290M, is NOT a LayerZero protocol bug. It's a configuration issue and a case study every project with a cross-chain token needs to look at today.
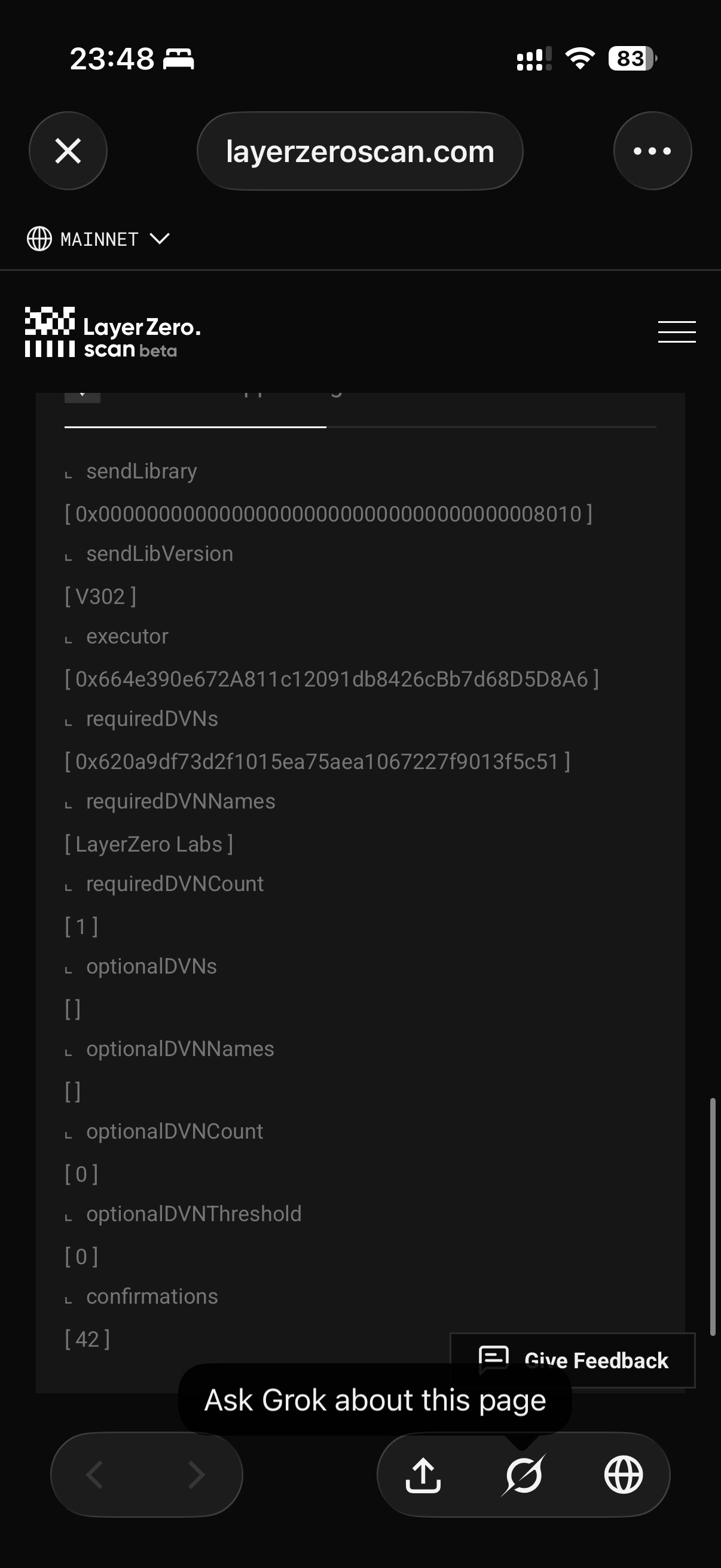
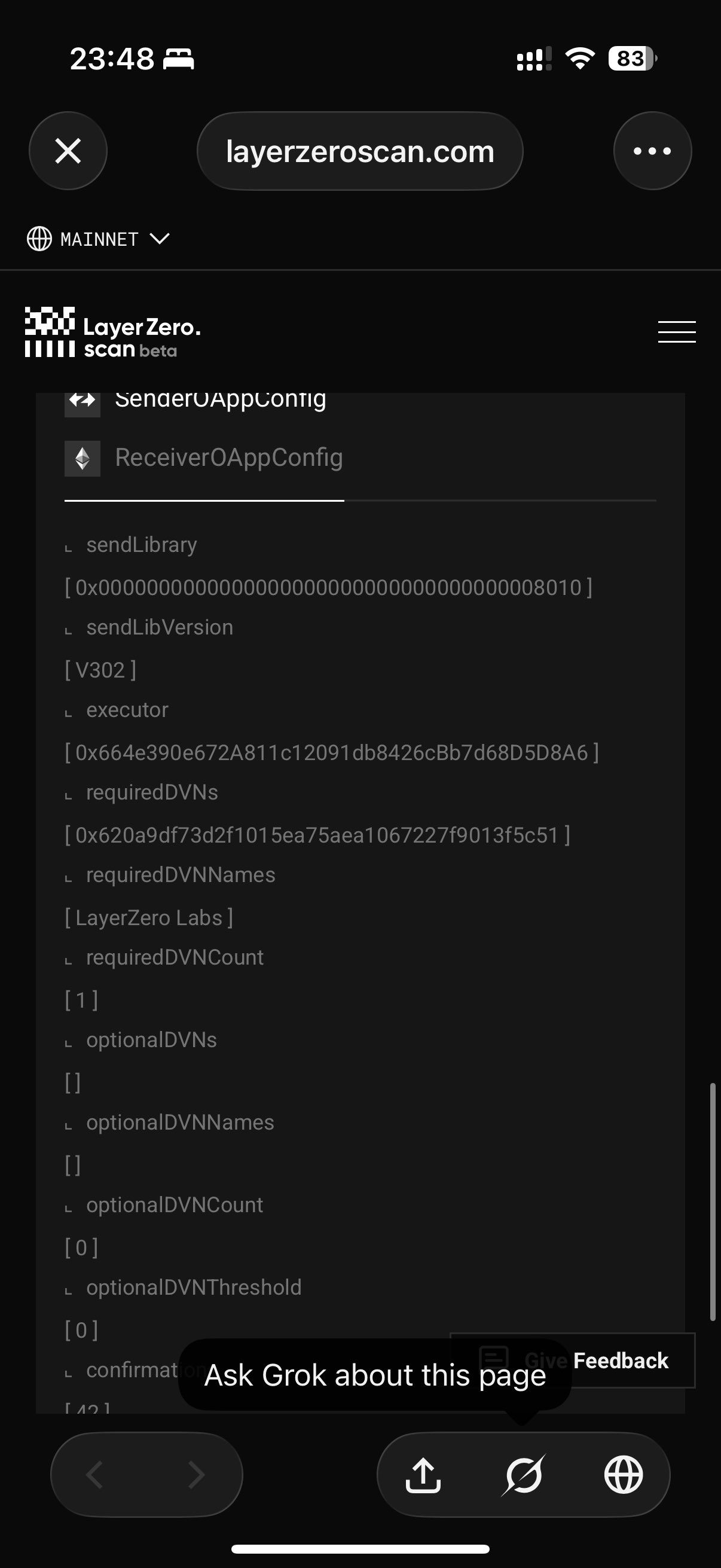
KelpDAO shipped their rsETH OFT with a 1/1 DVN security stack. One required verifier. Zero optional. Threshold 0. Straight from LayerZero Scan's ReceiverOAppConfig on the rsETH bridge pathway:
• requiredDVNCount: 1
• requiredDVNNames: [LayerZero Labs]
• optionalDVNCount: 0
• optionalDVNThreshold: 0
Source and Destination OApp both labeled "Kelp DAO." Destination is the rsETH OFT Adapter on Ethereum: 0x85d456B2DfF1fd8245387C0BfB64Dfb700e98Ef3.
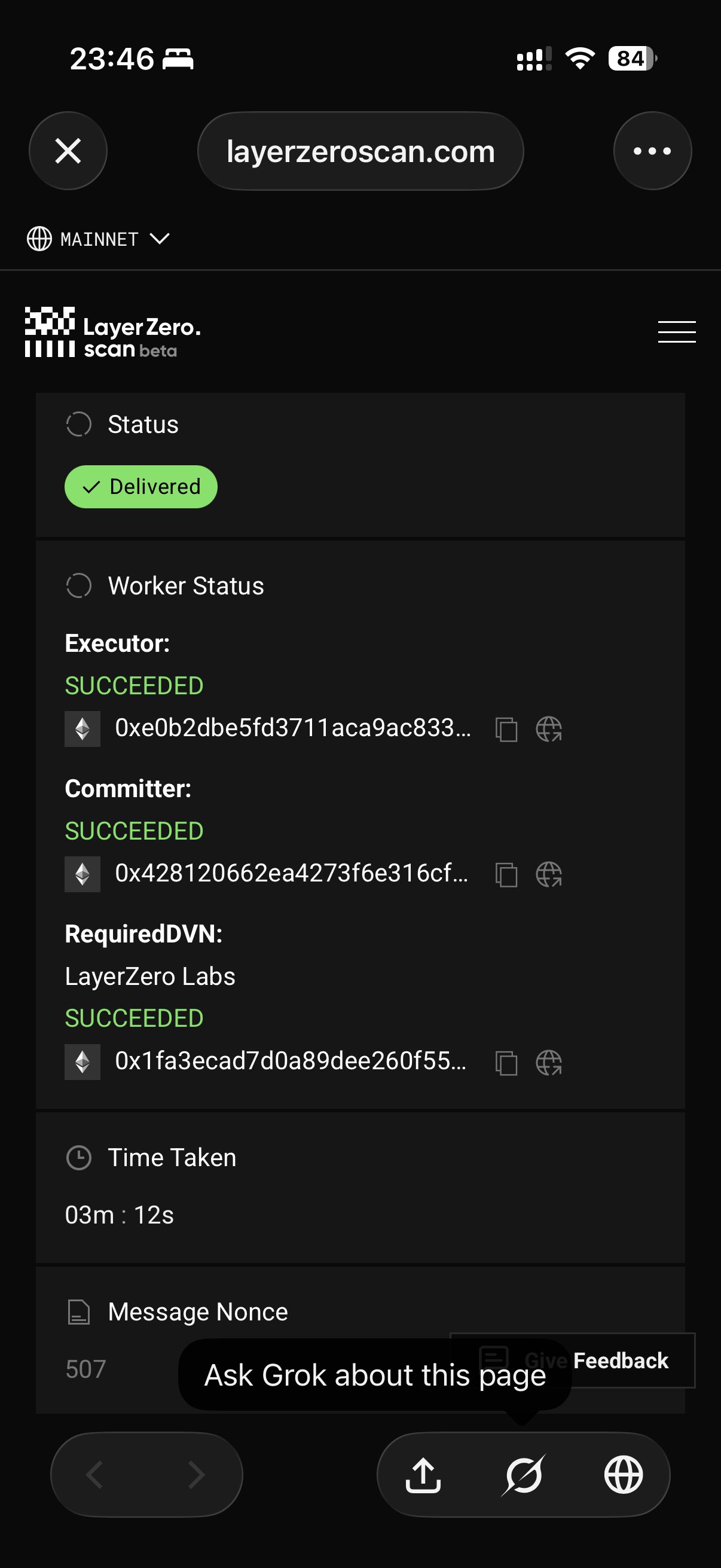
How the attack worked: the forged message's source packet was never actually emitted on the source chain (Unichain). The single required DVN signed an attestation for something that didn't exist and because it was the ONLY required DVN, there was no independent verifier to contradict it. Everything downstream then executed exactly as designed: commitVerification → lzReceive → peer check → OFT decode → rsETH mint. The contracts weren't broken. The verification layer was. One signature and 116,500 rsETH materialized out of thin air on Ethereum.
To be clear: LayerZero V2 is modular by design. Apps pick their own security stack X-of-Y-of-N, multiple independent DVNs, thresholds, block confirmations. No one is forced into any configuration. The protocol gave projects the full toolkit. KelpDAO chose 1/1.
Even reputable DVNs can have a bad day key compromise, infra failure, bad actor, whatever. That's exactly why you want multiple independent verifiers. Redundancy is the whole point. A 1/1 DVN is the cross-chain equivalent of a 1-of-1 multisig on a treasury.
Baseline for any OFT/OApp with serious TVL:
• Multiple required DVNs (3–4+)
• Independent providers (don't stack correlated risk) use canary DVN as it’s also its own independent client.
• Optional DVNs + threshold on top
• Sane block confirmations
If you're a founder or dev with an OFT live in production, pull your Send/Receive ULN config today. Call getConfig() on the endpoint. If requiredDVNCount is 1 and optionalDVNCount is 0, reconfigure before the market does it for you.
Anyone can verify any OApp's config on layerzeroscan.com right now.
Security is the application's responsibility. LayerZero hands every project a powerful, modular security stack it's on the project to actually use it. Kelp's full RCA is still coming, but the root enabler is already onchain and visible to anyone who looks.
Check your configs. Stay safe out there.