This new post from @LayerZero_Core directly contradicts Bryan's claim yesterday that the LayerZero Labs multisig signer who was trading the "McPepes" memecoin on Uniswap was just "testing the PEPE OFT integration"
Turns out that gaslighting doesn't work when people can check the chain and verify for themselves
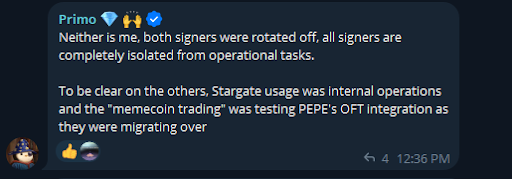
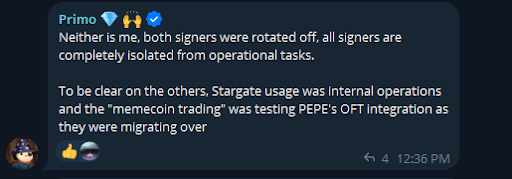
Naturally, they attempt to minimize the issue by making it seem like this was a one time incident, involving only one signing key, and that the memecoin trader was quickly rotated off the multisig
In reality, the multisig signer attempted multiple memecoin trades over the span of a year and stayed on the multisig for nearly two years after the first memecoin trade, before finally being rotated off
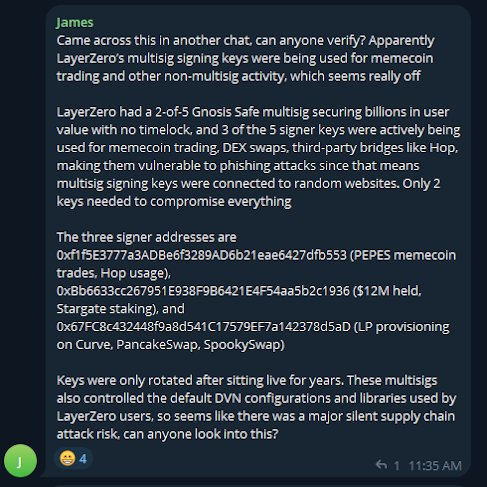
Furthermore, there were actually 3 signing addresses that were engaged in non-multisig related activity (memecoin trading, DEX swaps, bridging, LP provisioning) on a 2-of-5 Gnosis Safe multisig
Billions of dollars in OFT value was exposed to the risk of being exploited by a multisig whose majority threshold of signers failed to practice even the most basic opsec and key isolation practices, FOR YEARS
This was not a one-time error oopsie, this was a complete disregard for opsec
--
Timeline of events of the LayerZero memecoin trader multisig signer:
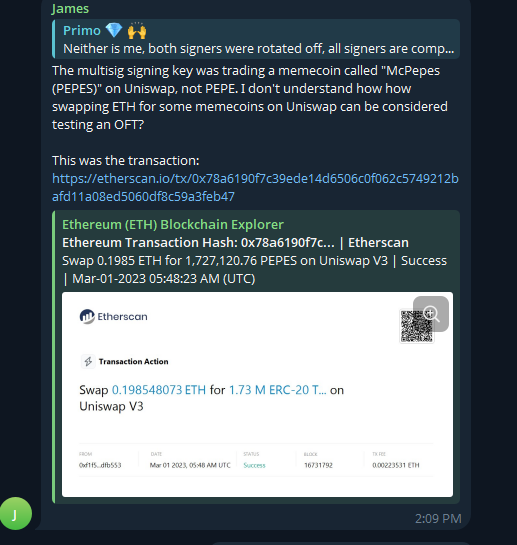
March 1, 2023 - 0xf1f5E swaps 0.198548 ETH for 1,727,120 McPepes (PEPES)
December 21, 2023 - 0xf1f5E calls approve() for Uniswap on the McPepes ERC20 contract
April 20, 2024 - 0xf1f5E attempts to sell McPepes on Uniswap but the transaction reverts
January 27, 2025 - 0xf1f5E is finally rotated off LayerZero’s Gnosis Safe multisigs and signing threshold changed
--
More context in following tweets
Overview on LayerZero multisig keys trading a memecoin called McPepes:
x.com/ChainLinkGod/status/205…
The multisig keys used in production by LayerZero Labs to secure billions in user funds was also being used to trade a memecoin called "McPepes (PEPES)"
... WTF
An absolute failure of even the most basic opsec and key isolation best practices, putting any user who used LayerZero's default config at risk of a supply chain attack as keys given the phishing risk
Bryan said they were testing "PEPE's OFT integration", but that's a completely different coin and has nothing to do with using production multisig keys to swap ETH for something called "McPepes" on Uniswap
PEPE hadn't even been deployed yet when this multisig signer was trading "McPepes"
The more that comes out about LayerZero Labs' irresponsible lack of opsec, the more I wonder how North Korea didn't infiltrate their infrastructure earlier, this is insane
Debates between Bryan and Ethereum community security researchers:
x.com/CatfishFishy/status/205…
Heeaaaaaaaaated debate broke out in the ETHSecurity Community Telegram earlier today between LayerZero’s Bryan and security researchers.
TLDR summary:
$3 billion+ of LZ OFTs were recently at risk of being compromised due to a default library contract that LZ Labs could upgrade instantly with no timelock to forge messages (like what happened with rsETH hack)-According to Banteg, major projects like Ethena and EtherFi were STILL using this default library contract as of a few weeks ago
There is still $178 million in value exposed to being compromised from projects using default library (look at quote tweet)
LZ Labs doesn’t need to be malicious for this be risk, they have history of poor opsec (in addition to being hacked by North Korea):
Onchain data shows LZ Labs multisig signers were engaging in non-multisig signing activity like trading memecoins, swapping on DEX, bridging. All major phishing risks as this mean production multisig keys were connected to websites, not just used for signing
LZ Labs handled private keys like a high schooler, trading memecoins on production multisig keys, no wonder they got targeted by North Korea, who knows what other poor opsec they have?
THREAD BELOW